Balancing Exploration and Exploitation in Materials Search Algorithms: Strategies for Accelerated Drug Discovery
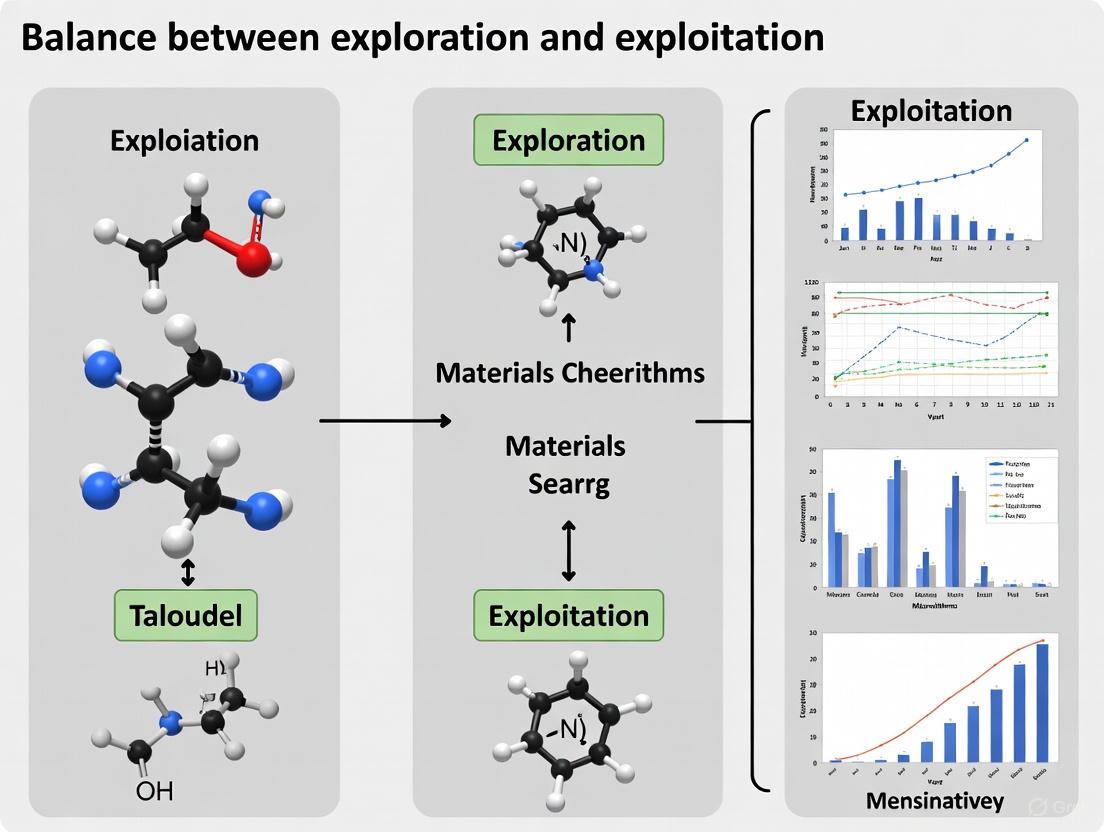
This article provides a comprehensive analysis of the exploration-exploitation trade-off, a critical challenge in optimizing materials search algorithms for drug development.
Balancing Exploration and Exploitation in Materials Search Algorithms: Strategies for Accelerated Drug Discovery
Abstract
This article provides a comprehensive analysis of the exploration-exploitation trade-off, a critical challenge in optimizing materials search algorithms for drug development. Tailored for researchers and pharmaceutical professionals, it covers foundational theory, modern algorithmic strategies like adaptive metaheuristics and multi-armed bandits, and practical solutions for overcoming local optima and premature convergence. It further details rigorous validation frameworks using benchmark functions and real-world case studies, offering a holistic guide for enhancing the efficiency and success rates of computational materials and drug candidate discovery.
The Fundamental Trade-Off: Understanding Exploration and Exploitation in Optimization
Frequently Asked Questions
1. What are the most common signs that my optimization algorithm is over-exploiting? A common sign is premature convergence, where the algorithm becomes trapped in a local optimum and the population of candidate solutions loses diversity. This is often characterized by a high number of duplicate solutions being evaluated and a stagnation in the improvement of the fitness score [1].
2. How can I balance exploration and exploitation in a multi-objective materials search? Balancing this trade-off is a central challenge. The Expected Hypervolume Improvement (EHVI) method has been demonstrated as an effective strategy. It actively manages the trade-off by selecting new data points that promise to increase the volume of the objective space dominated by the current Pareto front, thereby balancing the gain of new information (exploration) with the improvement of existing solutions (exploitation) [2].
3. My algorithm seems to be exploring randomly without improving. What should I check? This can indicate ineffective exploration. Investigate whether your algorithm's search mechanism is suited for the problem's fitness landscape. For deceptive landscapes with "blind spots" (global optima that are hard to find), algorithms may require enhanced exploration strategies, such as those incorporating Levy flight dynamics or memory mechanisms to avoid revisiting unproductive regions [3] [1].
4. What is a surrogate model and why is it used in materials informatics? A surrogate model is a machine learning model trained on existing data to rapidly predict material properties, acting as a stand-in for slower, more expensive experiments or simulations [4]. In an active learning loop, it is used to guide the search for new materials by identifying the most promising candidates to evaluate next, thus optimizing the use of resources [2].
Troubleshooting Guides
Problem: Algorithm Trapped in a Local Optimum (Over-Exploitation)
Description The algorithm converges too quickly on a sub-optimal solution, failing to discover better materials that may exist in other regions of the search space.
Diagnosis and Resolution Steps
- Quantify Population Diversity: Implement a method to track the diversity of your candidate solutions. A sharp decline in diversity is a key indicator of over-exploitation [1].
- Integrate a Memory Archive: Use a meta-approach like Long-Term Memory Assistance Plus (LTMA+). This technique maintains an archive of unique, non-revisited solutions and uses it to dynamically shift the search away from over-exploited regions and toward unexplored areas when stagnation is detected [1].
- Employ Advanced Search Strategies: Consider switching to or incorporating algorithms that use dynamic search patterns. For example, the Hare Escape Optimization (HEO) algorithm uses Levy flights and adaptive directional shifts to escape local optima effectively [3].
- Adjust Acquisition Function: If using Bayesian optimization, review your acquisition function. For a better exploration-exploitation balance, use a function like Expected Hypervolume Improvement (EHVI) instead of pure exploitation-based methods [2].
Problem: Inefficient Search in High-Dimensional Spaces (Poor Exploration)
Description The search process is slow, fails to find good solutions in a reasonable time, or misses the global optimum in a complex fitness landscape.
Diagnosis and Resolution Steps
- Benchmark on Deceptive Problems: Test your algorithm on specialized benchmark suites like the "Blind Spot" benchmark or functions from CEC 2015/2020. If performance is poor, it indicates a weakness in handling deceptive landscapes [1] [3].
- Enhance with Hybrid Strategies: Augment your base algorithm with a meta-layer like LTMA+. This helps improve robustness and success rates on problems where the global optimum is difficult to locate [1].
- Adopt a Modern Metaheuristic: Implement a recently developed algorithm designed for robust exploration, such as the Hare Escape Optimization (HEO), which has been validated on complex benchmarks and engineering problems [3].
- Validate with Multi-Objective Active Learning: For materials discovery, set up an active learning loop using multi-objective Bayesian optimization with EHVI. This has been proven to efficiently find optimal Pareto fronts by sampling only a small fraction (e.g., 16-23%) of the entire search space [2].
Experimental Protocols & Performance Data
Protocol 1: Active Learning with Multi-Objective Bayesian Optimization
This methodology is used for efficiently discovering materials that optimally satisfy multiple target properties [2].
- Database Construction: Compile a dataset of materials with the properties of interest. Example databases include the Computational 2D Materials Database (C2DB) or JARVIS-DFT.
- Feature Generation: Generate a numerical fingerprint or descriptor for each material in the dataset [4].
- Model Training: Train a separate surrogate model (e.g., a machine learning model) for each target property using the initial training data.
- Active Learning Loop:
- Using the surrogate models, identify the next most promising material candidate to evaluate. This is done by optimizing an acquisition function like EHVI.
- The new candidate is "sampled" (its properties are obtained via a high-fidelity calculation or experiment).
- This new data is added to the training set, and the surrogate models are retrained.
- The loop repeats until a stopping criterion is met (e.g., a performance target is reached).
Performance Data: The table below summarizes the efficiency of the EHVI method on a 2D materials database [2].
| Initial Training Data Ratio | Sampling of Search Space to Find Optimal Pareto Front |
|---|---|
| 0.5% | 16% |
| 1% | 19% |
| 5% | 23% |
Protocol 2: Benchmarking Algorithm Robustness with LTMA+
This protocol is used to evaluate and enhance an algorithm's ability to avoid premature convergence on difficult problems [1].
- Problem Selection: Use a benchmark designed to expose algorithmic weaknesses, such as the Blind Spot benchmark.
- Algorithm Setup: Configure the metaheuristic algorithm you wish to test.
- Integration with LTMA+: Enhance the algorithm with the LTMA+ meta-approach. This involves:
- Maintaining a long-term memory archive of unique solutions.
- Monitoring for duplicate solution evaluations.
- Using the frequency of duplicates to dynamically guide the search toward unexplored regions when diversity is low.
- Evaluation: Run the standard algorithm and the LTMA+-enhanced version on the benchmark. Compare success rates, solution accuracy, and convergence speed.
Performance Data: The table below shows the percentage speedup achieved by the original LTMA on different problem types [1].
| Problem Type | Speedup by LTMA |
|---|---|
| Low Computational Cost | ≥10% |
| Soil Model Optimization | ≥59% (35% duplicates generated without LTMA) |
The Scientist's Toolkit: Essential Research Reagents
In computational materials science, the "reagents" are the data, software, and algorithmic tools used to conduct research.
| Item Name | Function |
|---|---|
| High-Throughput Data Repositories (e.g., Materials Project, NOMAD) | Provides reliable, large-scale data on material properties for training surrogate models and benchmarking [4]. |
| Numerical Fingerprints/Descriptors | Converts a material's chemical structure into a numerical string, enabling machine learning [4]. |
| Surrogate Machine Learning Models | Enables rapid prediction of material properties without expensive simulations, accelerating the search loop [4] [2]. |
| Acquisition Functions (e.g., EHVI) | In Bayesian optimization, this function decides the next experiment to run by balancing exploration and exploitation [2]. |
| Specialized Benchmarks (e.g., CEC suites, Blind Spot) | Provides standardized test problems to evaluate, validate, and compare the performance of optimization algorithms [3] [1]. |
Workflow and Relationship Diagrams
Diagram 1: Active Learning Loop in Materials Search
Diagram 2: Troubleshooting Over-Exploitation with LTMA+
For researchers in materials science and drug development, computational search algorithms are indispensable for navigating vast, complex search spaces to discover new compounds or optimize molecular structures. The performance of these algorithms hinges on a fundamental trade-off: exploration, the broad investigation of new regions of the search space, and exploitation, the intensive refinement of known promising areas [5]. An imbalance can lead to excessive computational costs or premature convergence on suboptimal solutions. This technical support center provides practical guides and FAQs to help you diagnose and resolve common issues related to this critical balance in your experiments.
Troubleshooting Guides
Guide 1: Diagnosing and Correcting Search Stagnation
Problem: Your algorithm's performance has plateaued, and it is no longer finding improved solutions.
Diagnostic Steps:
- Check Population Diversity: Monitor the diversity of your candidate solutions in both the search (e.g., genetic sequences, chemical descriptors) and objective (e.g., binding affinity, material property) spaces over generations. A rapid decline indicates excessive exploitation [6].
- Analyze Acceptance Rate: Track the rate at which new, worse-performing solutions are accepted. A rate that drops to zero too early suggests the algorithm cannot escape local optima [5].
Solutions:
- For Excessive Exploitation (Stuck in Local Optima):
- Increase Exploration Parameters: In Simulated Annealing, increase the initial temperature or slow the cooling rate. In Tabu Search, increase the tabu list size [5].
- Introduce a Hybrid Operator: If using a multi-operator algorithm, dynamically increase the usage of exploratory operators (e.g., DE/rand/1/bin) when stagnation is detected [6].
- Implement Random Restarts: Periodically re-initialize part of the population from random points in the search space to rediscover diversity [5].
- For Excessive Exploration (Slow Convergence):
- Increase Exploitation Parameters: Lower the initial temperature in Simulated Annealing or use a more aggressive cooling schedule. In population-based algorithms, reduce the mutation rate [5].
- Switch to Local Search: After an initial exploratory phase, hybridize your algorithm with a local search method to intensively exploit the best regions found [5].
Guide 2: Tuning Algorithm Parameters for Specific Search Landscapes
Problem: Your algorithm performs well on standard test functions but fails on your specific research problem.
Diagnostic Steps:
- Characterize Your Landscape: Analyze your problem's fitness landscape. Is it smooth or rugged? Are there many local optima? This understanding guides parameter selection.
- Perform Sensitivity Analysis: Systematically run your algorithm while varying one key parameter (e.g., mutation rate, cooling rate) at a time to observe its impact on final solution quality and convergence speed [6].
Solutions:
- For Rugged Landscapes (Many local optima): Prioritize exploration. Use higher mutation rates, higher initial temperatures, and consider algorithms like Tabu Search that explicitly forbid revisiting recent solutions [5].
- For Smooth Landscapes: Prioritize exploitation. Use lower mutation rates and algorithms like Hill Climbing that can efficiently refine a good solution [5].
- Implement Adaptive Tuning: Use a strategy that dynamically adjusts parameters based on search progress, such as reducing the mutation rate as the population converges or using survival analysis to choose between exploratory and exploitative operators [6].
Frequently Asked Questions (FAQs)
Q1: How can I quantitatively measure the exploration-exploitation balance in my algorithm during a run? A1: Direct measurement is challenging, but effective proxies exist. You can track the population diversity in the search space (e.g., average Hamming distance between genotypes, variance in continuous parameters) – high diversity suggests exploration. Conversely, monitoring the rate of improvement in fitness can indicate exploitation. Some advanced methods propose indicators like "Survival length in Position (SP)" to guide this balance adaptively [6].
Q2: My multiobjective evolutionary algorithm (MOEA) finds a diverse Pareto front, but the solutions are not close to the true optimum. Is this an exploration or exploitation problem? A2: This is typically an exploitation problem. The algorithm is successfully exploring different regions of the objective space (good diversity) but failing to refine the solutions within those regions to push them closer to the true Pareto front. To address this, enhance exploitation by incorporating local search operators around promising solutions on the front, or using recombination operators that favor small, refinements [6].
Q3: In Simulated Annealing, what is a good rule of thumb for setting the initial temperature and cooling rate? A3: While problem-specific, a common methodology is to choose an initial temperature that allows for a high probability (e.g., 80%) of accepting a worse solution of a typical magnitude early in the search. The cooling rate is often set between 0.95 and 0.99, applied multiplicatively each iteration, providing a gradual shift from exploration to exploitation. The exact values should be determined empirically for your problem [5].
Q4: How does the trade-off differ between single-objective and multiobjective optimization? A4: In single-objective optimization, population diversity in the search space is typically allowed to decrease over time to converge on a single optimum. In multiobjective optimization, diversity must be maintained throughout the search in the objective space to capture a representative Pareto front, even while exploitation is used to improve the convergence of each solution on the front [6].
Experimental Protocols & Data
Table 1: Characteristics and trade-offs of common local search algorithms.
| Algorithm | Primary Strength | Mechanism for Exploration | Mechanism for Exploitation | Best Suited For |
|---|---|---|---|---|
| Hill Climbing | Simplicity, fast convergence | None (greedy) | Always moving to a better neighbor | Smooth, unimodal landscapes [5] |
| Simulated Annealing | Escaping local optima | Accepting worse moves at high temperature | Greedy acceptance at low temperature | Rugged landscapes with many local optima [5] |
| Tabu Search | Avoiding cycles | Tabu list forbids recent moves | Intensive local search on current solution | Complex constraints and path-based problems [5] |
| Multiobjective EA (EMEA) | Balanced Pareto front discovery | DE recombination operator | Clustering-based advanced sampling | Problems requiring a diverse, high-quality solution set [6] |
Detailed Methodology: Simulated Annealing for Materials Search
This protocol outlines the implementation of a Simulated Annealing algorithm to find a material composition with a target property [5].
1. Initialization:
- Define an objective function,
F(x), that quantifies the performance of a material compositionx(e.g., superconducting critical temperature). - Initialize a random starting solution
current_x. - Set parameters:
initial_temp = 1000,cooling_rate = 0.003, andmax_iterations = 5000.
2. Iterative Search:
For each iteration up to max_iterations:
- Generate Neighbor: Create a new solution
neighbor_xby perturbingcurrent_x(e.g., slightly altering elemental dopant concentrations). - Evaluate: Calculate
current_score = F(current_x)andneighbor_score = F(neighbor_x). - Acceptance Probability: Decide whether to move to the neighbor:
- If
neighbor_scoreis better, always accept. - If
neighbor_scoreis worse, accept with probabilityP = exp((current_score - neighbor_score) / current_temp).
- If
- Update Best: If
current_scoreis the best found so far, record it. - Cool Down: Update the temperature:
current_temp = current_temp * (1 - cooling_rate).
3. Output: Return the best solution found during the search.
Workflow Visualization
The following diagram illustrates the logical flow and balancing mechanism of the Simulated Annealing protocol.
The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential computational "reagents" for search algorithm experiments.
| Item / Concept | Function in the Experiment |
|---|---|
| Objective Function | The "assay" that quantifies the quality of a candidate solution (e.g., predicted binding affinity, material density) [5]. |
| Recombination Operator (e.g., DE/rand/1/bin) | An exploratory operator that creates new solutions by combining parts of existing ones, promoting genetic diversity in the population [6]. |
| Local Search Operator (e.g., Hill Climbing) | An exploitative operator that refines a single solution by searching its immediate neighborhood for incremental improvements [5]. |
| Temperature Parameter (Simulated Annealing) | A dynamic control knob that explicitly manages the trade-off. High values favor exploration (accepting worse moves), low values favor exploitation [5]. |
| Tabu List (Tabu Search) | A memory structure that prevents the algorithm from revisiting recently explored solutions, forcing exploration of new regions [5]. |
| Survival Analysis Indicator | A probabilistic metric used in adaptive algorithms to decide whether to invoke an exploratory or exploitative operator based on recent search progress [6]. |
FAQs: Multi-Armed Bandit Implementation for Materials Research
Q1: What is the core exploration-exploitation dilemma in the context of materials science? The Multi-Armed Bandit (MAB) problem models the challenge of choosing between exploring new options with uncertain rewards and exploiting the best-known option. In materials science, this translates to the challenge of balancing research efforts between testing new, unexplored material compositions (exploration) and further investigating the most promising known candidates (exploitation) to maximize the discovery of materials with desired properties within a limited research budget [7] [8].
Q2: How do I choose between algorithms like ε-Greedy, UCB, and Thompson Sampling for my search? The choice of algorithm depends on your specific project's needs for simplicity, performance, and handling of uncertainty. The following table summarizes the key characteristics:
| Algorithm | Core Mechanism | Best For | Key Considerations |
|---|---|---|---|
| ε-Greedy [8] [9] | Selects random action with probability ε, otherwise greedy action. | Simple, easy-to-implement baselines. | Fixed exploration rate can be inefficient; performance sensitive to ε value. |
| Upper Confidence Bound (UCB) [8] [9] | Selects action with highest upper confidence bound on reward. | Scenarios favoring optimism under uncertainty. | Deterministic; requires tracking all arms. UCB1 form: $Q(a) + \sqrt{\frac{2 \log t}{N_t(a)}}$ [8]. |
| Thompson Sampling [8] [9] | Draws reward samples from posterior (e.g., Beta) distributions, picks best. | Efficiently balancing exploration/exploitation; Bernoulli rewards. | Probabilistic; often delivers superior empirical performance. Beta posterior update [8]. |
Q3: My material search space is vast and high-dimensional. Can MAB methods handle this? Standard MABs treat each "arm" as independent, which is inefficient for vast chemical spaces. For these problems, Contextual Bandits are more suitable. They incorporate feature vectors (e.g., molecular descriptors, elemental properties) into the decision-making process, allowing the algorithm to generalize learning from one material to other, structurally similar materials. This enables a more intelligent search across the entire space [10] [11]. Advanced methods like the Mendelevian Search (MendS) algorithm use a double evolutionary search through this abstract chemical space to find optimal compounds [12].
Q4: What are the common pitfalls when applying a MAB framework to clinical dose-finding trials? A key challenge in dose-finding is the small sample size, which can lead to high variability in reward estimates. For instance, in Thompson Sampling, the heavy tails of the posterior distribution can cause erratic dose selection. Mitigation strategies include Regularized Thompson Sampling or switching to a greedy algorithm that selects based on the posterior mean rather than a random sample, which can improve stability and performance in these limited-data environments [13].
Q5: How can I address the computational cost of MAB algorithms with many material options? Scalability is a known challenge. Strategies to manage this include:
- Algorithm Choice: Simpler algorithms like ε-Greedy have lower computational overhead than Thompson Sampling [9].
- Feature-Based Approaches: Using Contextual Bandits to generalize rather than treat each arm independently [11].
- Parallelization: Where possible, design experiments to allow for parallel evaluation of multiple candidates to accelerate data collection.
Troubleshooting Guides
Guide 1: Resolving Premature Convergence to a Suboptimal Material
Problem: Your algorithm is repeatedly selecting the same material candidate early in the search process, potentially missing better options.
Solution Steps:
- Diagnose the Exploration Rate:
- For ε-Greedy, check if the value of ε is too low. A very small ε (e.g., <0.01) leads to minimal exploration [9].
- For Thompson Sampling, examine the posterior distributions. If they prematurely converge with very low variance, the algorithm will stop exploring.
Adjust Algorithm Parameters:
Validate the Reward Function: Ensure your reward function (e.g., a measure of material hardness) is correctly calibrated and provides a meaningful signal for the property you are optimizing [10].
Guide 2: Managing Noisy or Sparse Material Property Data
Problem: Experimental data for material properties can be noisy, sparse, and high-dimensional, which undermines the algorithm's ability to learn accurate reward models [10].
Solution Steps:
- Incorporate Domain Knowledge: Use feature representations (descriptors) for your materials that are informed by domain expertise. This helps the algorithm reason about similarities between different material compositions [10] [11].
- Leverage Probabilistic Models: Algorithms like Thompson Sampling are naturally suited for noisy environments because they maintain a distribution over reward estimates, explicitly modeling uncertainty [8] [9].
- Implement Bayesian Optimization: For inverse materials design (finding materials given desired properties), Bayesian optimization, which often uses Thompson Sampling-like acquisition functions, is a standard and powerful tool for navigating noisy, expensive-to-evaluate objective functions [10].
Experimental Protocols & Workflows
Protocol 1: Implementing a Thompson Sampling Bandit for Compound Screening
Objective: To identify the compound with the highest success probability (e.g., binding affinity, catalytic activity) from a library of K candidates.
Methodology:
- Initialization:
Iterative Experimentation (for each round t):
- Sample: For each arm ( k ), draw a sample ( \thetak ) from its current Beta(( \alphak ), ( \beta_k )) distribution [9].
- Select: Choose the arm ( at ) with the largest sampled value ( \thetak ) [9].
- Experiment: Perform the experiment (e.g., assay) on the selected compound ( a_t ).
- Observe Reward: Record the outcome ( rt ), where ( rt = 1 ) for a success and ( 0 ) for a failure [9].
- Update: Update the parameters for the selected arm ( at ):
Termination: The process is repeated until a predetermined budget (number of experiments) is exhausted. The arm with the highest empirical success rate (( \alphak / (\alphak + \beta_k) )) is reported as the best candidate.
The workflow for this protocol is illustrated in the following diagram:
Protocol 2: Mendelevian Search for Inverse Materials Design
Objective: To discover the compound and crystal structure with the optimal value for a target property (e.g., hardness, magnetization) across all possible combinations of chemical elements [12].
Methodology:
- Define Chemical Space: Construct an abstract chemical space where proximity correlates with similarity in material properties [12].
- Double Evolutionary Search:
- Inner Loop (Structure Prediction): For a given point in chemical space (a composition), an evolutionary algorithm searches for the most stable crystal structure [12].
- Outer Loop (Composition Search): The discovered compounds compete, "mate," and "mutate" within the chemical space, evolving towards regions with superior target properties [12].
- Selection: The algorithm selects the best material based on the evolutionary process, effectively solving the inverse design problem.
The Scientist's Toolkit: Key Research Reagents & Computational Solutions
This table details essential computational "reagents" for implementing bandit-based search strategies.
| Item / Solution | Function / Explanation | Application Example |
|---|---|---|
| Beta Distribution | A continuous probability distribution on [0, 1], used as a conjugate prior for Bernoulli rewards in Bayesian analysis. | Modeling the posterior distribution of a success probability (e.g., drug efficacy, reaction yield) in Thompson Sampling [8] [9]. |
| Markov Decision Process (MDP) | A mathematical framework for modeling sequential decision-making under uncertainty where outcomes are partly random and partly under control. | Formally defining the state, actions, and transition dynamics of a bandit problem, especially for more complex variants like restless bandits [7]. |
| Gittins Index | A dynamic allocation index that provides the optimal solution for the infinite-horizon discounted Bayesian MAB problem [7] [14]. | Optimizing resource allocation in theoretical models, though rarely used in clinical trials due to low statistical power for hypothesis testing [14]. |
| Contextual Feature Vector | A set of numerical descriptors representing the features of a candidate (e.g., molecular weight, atomic radius, electronic band gap). | Enabling Contextual Bandits to generalize learning across the material search space by relating arm choice to observable features [11]. |
| High-Throughput Virtual Screening (HTVS) | A computational method to rapidly screen vast libraries of material candidates using simulations to generate data [10]. | Generating initial data on material properties to train or provide a prior for bandit algorithms, reducing the number of physical experiments needed [10]. |
Core Concepts: Exploration vs. Exploitation in Drug Discovery
In the context of drug discovery, the challenge of exploration (searching for new, promising candidate molecules) versus exploitation (optimizing known, high-value leads) is a central computational problem [15]. AI-driven methods have transformed this search process, enabling researchers to navigate the vast chemical space of potential drug candidates more efficiently than ever before [16] [17].
Exploration is the process of choosing actions with the objective of learning about the environment. In drug discovery, this involves screening vast chemical libraries or using generative AI to design novel molecular structures to identify initial "hit" compounds [16] [18]. Exploitation, on the other hand, is the process of using previously obtained information to acquire rewards. This translates to optimizing the chemical structure of a confirmed "hit" or "lead" compound to enhance its potency, selectivity, and safety profile [16]. Optimal strategies will combine these two objectives appropriately [15].
The table below summarizes how this balance manifests in key stages of the drug discovery pipeline.
| Discovery Stage | Exploration (Broad Search) | Exploitation (Focused Optimization) |
|---|---|---|
| Target Identification | Identifying novel biological targets (e.g., proteins, genes) for a disease [16]. | Validating and deepening understanding of a known, high-value target [16]. |
| Hit Identification | Virtual screening of ultra-large libraries (billions of compounds) to find initial "Hits" [17]. | Iterative testing and confirmation of a small set of promising candidate "Hits" [16]. |
| Lead Optimization | Generating diverse analog structures around a Lead compound to explore chemical space [16]. | Fine-tuning the Lead's structure to improve specific properties like potency and metabolic stability [16]. |
Troubleshooting Guides & FAQs
This section addresses common operational challenges when implementing algorithmic search strategies in a drug discovery environment.
FAQ: Algorithmic Search & Balance
What does "balancing exploration and exploitation" mean in a practical screening campaign? It means strategically allocating computational and experimental resources. For example, an initial campaign might use fast, lower-fidelity filters (e.g., simple docking) to explore a billion-compound library (exploration). Promising hits from this round are then fed into a more computationally expensive, high-fidelity simulation (exploitation) to select the best few hundred compounds for synthesis and testing [17]. The optimal strategy combines these two objectives to be both informative and rewarding [15].
How can I tell if my screening algorithm is over-exploiting? A key sign is a lack of chemical diversity in the final output. If all your top-ranked compounds are structurally very similar, your algorithm may be stuck in a local optimum and failing to explore other promising regions of chemical space. This can be formalized using the Z'-factor, which assesses data quality; a large assay window with high noise (poor Z'-factor) may indicate ineffective exploration or unstable results [19].
We use AI for molecular design. How does exploration/exploitation apply? Generative AI models, like Generative Adversarial Networks (GANs), directly embody this balance [16]. The generator creates new molecular structures (exploration), while the discriminator evaluates them against known desirable properties (exploitation). This adversarial process continues until the generator produces optimized, novel compounds [16].
Troubleshooting Common Experimental Issues
Problem: No Assay Window in a TR-FRET-Based Screening Assay
- Description: The assay fails to show a meaningful signal difference between positive and negative controls.
- Solution:
- Verify Instrument Setup: The most common reason is an incorrect instrument configuration. Confirm that the exact recommended emission and excitation filters for your TR-FRET assay are used [19].
- Check Reagent Quality: Ensure assay reagents, such as the Terbium (Tb) or Europium (Eu) donors, have not degraded and are pipetted accurately [19].
- Test Reader Setup: Use purchased reagents to perform a plate reader validation test before running your actual assay [19].
Problem: High Variation (Noise) in Screening Data
- Description: Data points show large standard deviations, making it difficult to distinguish true hits from background noise.
- Solution:
- Use Ratiometric Data Analysis: For TR-FRET assays, always use the emission ratio (Acceptor Signal / Donor Signal, e.g., 520 nm/495 nm for Tb) instead of raw RFU values. This accounts for pipetting variances and lot-to-lot reagent variability [19].
- Calculate the Z'-Factor: Assess assay robustness with the Z'-factor. A value >0.5 is considered suitable for screening. This metric considers both the assay window and the data variation [19].
- The formula is:
Z' = 1 - [ (3 * SD_positive + 3 * SD_negative) / |Mean_positive - Mean_negative| ][19].
Problem: Inconsistent EC50/IC50 Values Between Labs
- Description: Different laboratories obtain differing potency values for the same compound.
- Solution:
- Audit Stock Solutions: The primary reason is differences in the preparation of compound stock solutions (e.g., at 1 mM). Verify solubility, concentration, and storage conditions [19].
- Consider Biological Context: In cell-based assays, the compound may not effectively cross the cell membrane or may be affecting an upstream/downstream target. Confirm the assay is measuring the intended interaction [19].
Experimental Protocols
Protocol 1: Iterative Ultra-Large Virtual Screening
This methodology accelerates the discovery of novel hit compounds from gigascale chemical libraries by balancing broad exploration with focused exploitation [17].
Library Preparation (Exploration Setup):
- Start with an ultra-large virtual chemical library (e.g., ZINC20, Enamine REAL) containing billions of readily synthesizable molecules [17].
- Prepare the library for docking by generating 3D conformational structures and applying standard drug-like filters.
Initial Broad Docking (Exploration Phase):
- Perform a fast, first-pass molecular docking screen against your protein target's 3D structure for the entire library. This step prioritizes breadth over precision [17].
Iterative Refinement & Screening (Exploitation Phase):
- Select the top 1-10 million compounds from the initial screen.
- Re-dock this subset using more sophisticated, computationally expensive methods (e.g., more precise scoring functions, molecular dynamics simulations) [17].
- Further refine the selection through multiple iterative rounds, potentially incorporating active learning, where the model prioritizes compounds it is most uncertain about, balancing exploration and exploitation [17].
Final Selection & Validation:
- Select a few hundred to a thousand top-ranking compounds for in vitro experimental testing.
- Confirm "hits" through dose-response assays to determine IC50/EC50 values.
Protocol 2: AI-Driven de Novo Molecular Design
This protocol uses generative models to create novel, optimized drug candidates from scratch [16].
Model Training (Learning the Chemical Space):
- Train a deep learning model, such as a Generative Adversarial Network (GAN) or a variational autoencoder (VAE), on a large dataset of known drug-like molecules and their properties [16].
- The generator learns to produce novel molecular structures, while the discriminator learns to distinguish them from real ones [16].
Conditional Generation (Guided Exploitation):
Molecular Generation & Filtering (Exploration Phase):
- Use the trained generator to produce a large library of novel candidate molecules.
- Filter this generated library using predictive AI models (e.g., for toxicity, synthetic accessibility) to remove unrealistic or undesirable compounds [16].
Optimization & Selection (Exploitation Phase):
- Employ reinforcement learning or Bayesian optimization to iteratively improve the generated structures against a multi-parameter optimization goal (e.g., potency + selectivity + solubility) [16].
- Select the final, top-ranked molecules for synthesis and biological testing.
Workflow & Pathway Diagrams
AI-Driven Drug Discovery Workflow
Exploration vs. Exploitation Balance
The Scientist's Toolkit: Research Reagent Solutions
The following table details key computational and experimental resources essential for implementing AI-driven discovery campaigns.
| Tool / Reagent | Function / Description | Role in Exploration/Exploitation |
|---|---|---|
| ZINC20 / Enamine REAL | Free and commercial ultralarge databases of readily synthesizable compounds for virtual screening [17]. | Exploration: Provides the chemical space for initial broad screening. |
| Generative Adversarial Network (GAN) | A deep learning model consisting of a generator (creates molecules) and a discriminator (evaluates them) [16]. | Core Balance: The generator explores, the discriminator exploits. |
| AlphaFold | AI system that predicts the 3D structure of proteins from their amino acid sequence [18]. | Enabler: Provides structural data for structure-based screening (both exploration and exploitation). |
| LanthaScreen TR-FRET Assays | Homogeneous assays used for high-throughput screening and profiling compound activity (e.g., kinase inhibition) [19]. | Exploitation: Provides high-quality experimental data for validating and optimizing hits/leads. |
| Quantitative Structure-Activity Relationship (QSAR) | Modeling approach that relates a compound's molecular descriptors to its biological activity [16]. | Exploitation: Uses known data to predict and optimize the activity of new analogs. |
Algorithmic Strategies for Dynamic Balance: From Epsilon-Greedy to Adaptive Metaheuristics
Frequently Asked Questions
Q1: My Epsilon-Greedy algorithm converges to a sub-optimal arm. What is the most likely cause and how can I fix it? A1: This occurs when the exploration rate (ε) is set too high, causing excessive random exploration long after the optimal arm is identified [20]. To fix this:
- For stationary problems (where reward distributions do not change), use a decaying ε schedule or an annealing strategy to reduce exploration over time [21] [22].
- For non-stationary problems, a constant ε may be necessary; tune its value carefully via simulation to balance exploration and exploitation for your specific environment [23].
Q2: How does the UCB algorithm avoid the need for a manually set exploration parameter like epsilon? A2: UCB automatically balances exploration and exploitation by constructing a confidence bound for each arm's reward estimate. It selects the arm that maximizes the sum of the estimated reward (exploitation) and a confidence term (exploration). This confidence term is large for arms that have been sampled infrequently or when the total number of trials is low, ensuring they are explored. The exploration naturally decays as an arm is pulled more often [24] [25] [20].
Q3: In a materials search with a limited experimental budget, which algorithm typically finds the highest-performing candidate faster? A3: For problems with a large number of arms (candidates) and a limited budget, UCB or Thompson Sampling often outperform the standard Epsilon-Greedy algorithm. UCB's targeted exploration is more efficient than Epsilon-Greedy's random exploration, which wastes trials on clearly suboptimal arms [26]. The following table summarizes a comparative experiment highlighting this performance difference.
| Algorithm | Number of Sockets | Mean Reward Spread | Time Steps to Reach Target Charge | Key Observation |
|---|---|---|---|---|
| Epsilon-Greedy | 5 | 2.0 | ~320 | Performs adequately with few, distinct options [26]. |
| UCB | 5 | 2.0 | ~300 | Quickly identifies and exploits the best arm [26]. |
| Epsilon-Greedy | 100 | 0.1 | >500 (Did not finish in time) | Struggles with many similar options due to inefficient random exploration [26]. |
| UCB | 100 | 0.1 | ~400 | More efficient than Epsilon-Greedy, but slowed by initial "priming rounds" [26]. |
| Thompson Sampling | 100 | 0.1 | ~350 | Best performance in complex scenarios, requiring no parameter tuning [26]. |
Q4: What is a major drawback of the purely Greedy algorithm in a research context? A4: The purely Greedy algorithm often converges to a local optimum (sub-optimal material) because it exploits the first arm that appears good and never explores alternatives. Its performance is highly sensitive to initial reward estimates, which can be problematic with no prior knowledge [27] [20].
Experimental Protocols & Methodologies
Below is a detailed protocol for comparing Epsilon-Greedy and UCB1 algorithms, based on established testing frameworks [27] [26].
1. Objective To empirically evaluate and compare the performance, in terms of cumulative regret and optimal action identification, of the Epsilon-Greedy and UCB1 algorithms on a stochastic multi-armed bandit problem.
2. Materials & Setup (The Researcher's Toolkit) The core components required to implement this experimental protocol are software-based.
| Research Reagent / Tool | Function / Description |
|---|---|
| k-Armed Bandit Testbed | A simulated environment with a set of 'k' arms (e.g., material candidates). Each arm returns a reward from a fixed probability distribution when pulled [23]. |
| Reward Distribution (Normal) | Used to model stochastic rewards for each arm. The mean (μ) represents the arm's true performance, and the standard deviation (σ) represents noise or measurement error [24] [23]. |
| Algorithm Implementations | Code for the Epsilon-Greedy and UCB1 selection policies. This includes the logic for updating reward estimates and selecting the next arm [27]. |
| Performance Metric: Cumulative Regret | The primary metric, calculated as the sum over time of the difference between the reward of the optimal arm and the reward of the arm selected by the algorithm [24]. |
3. Procedure
- Initialize the Bandit Problem:
Initialize the Algorithms:
- Epsilon-Greedy: Set the exploration parameter ε (e.g., ε=0.1). Initialize the estimate ( Q(a) ) for each arm to 0 and the count ( N(a) ) to 0 [27] [23].
- UCB1: Set the confidence level parameter c (a common value is c=√2). Initialize ( N(a) ) to 0. Perform a priming round by pulling each arm once to obtain initial ( Q(a) ) estimates [27] [24].
Run the Experiment for T Time Steps:
- For t = 1 to T (e.g., T=1000):
- Epsilon-Greedy:
- With probability (1-ε), select the greedy arm: ( At = \arg\maxa Q(a) ).
- With probability ε, select a random arm uniformly.
- UCB1:
- Select the arm that maximizes: ( Q(a) + c \times \sqrt{\frac{\log(t)}{N(a)}} ).
- For the selected arm ( At ), receive a reward ( Rt ) from the environment.
- Update the estimates for ( At ):
- Increment the count: ( N(At) = N(At) + 1 ).
- Update the value estimate incrementally: ( Q(At) = Q(At) + \frac{1}{N(At)} (Rt - Q(At)) ) [23].
- Epsilon-Greedy:
- Record the reward and whether the optimal arm was selected at each step.
- For t = 1 to T (e.g., T=1000):
Repeat and Average:
- Repeat the entire experiment for a large number of independent runs (e.g., 1000) with different randomly generated bandit problems to obtain statistically significant results [23].
- Calculate the average reward and percentage of time the optimal arm was selected across all runs for each time step.
4. Expected Results & Analysis
- The Epsilon-Greedy algorithm will show linear cumulative regret, ( O(T) ), because it continues to explore at a fixed rate [24].
- The UCB1 algorithm will show logarithmic cumulative regret, ( O(\log T) ), as it efficiently reduces exploration over time, leading to better long-term performance [24].
- You should generate a plot of Average Reward vs. Steps and % Optimal Action vs. Steps. The UCB1 curve will typically rise faster and stabilize at a higher level than the Epsilon-Greedy curve, especially with well-tuned parameters [23].
Algorithm Logic and Workflow
The following diagram illustrates the core decision-making logic of the UCB1 algorithm, which embodies the principle of "optimism in the face of uncertainty."
UCB1 Algorithm Decision Flow
Troubleshooting Guide
Problem: UCB1 performs poorly in early stages with many arms. Solution: This is due to the mandatory "priming rounds" where each of the k arms is pulled once. For a very large k, this initial exploration phase is long. Consider algorithms like Thompson Sampling that do not have this requirement and can start exploiting promising arms more quickly [26].
Problem: Choosing the right parameters (ε for Epsilon-Greedy, c for UCB1) is difficult. Solution:
- For Epsilon-Greedy, a common starting point is ε=0.1. For a more robust approach, implement epsilon annealing, where ε starts higher and decays over time (e.g., ε = 1/√t) [21].
- For UCB1, the theoretical value ( c = \sqrt{2} ) is a good default. If performance is suboptimal, perform a parameter sweep on a simulated version of your problem to find a better value [25].
Problem: My reward distributions are changing over time (non-stationary). Solution: Both basic algorithms assume stationary distributions. To handle non-stationarity:
- Use a constant step-size parameter α instead of 1/N(a) when updating Q(a). This gives more weight to recent rewards, allowing the algorithm to forget old data and adapt to changes [23].
- Explore more advanced bandit algorithms specifically designed for non-stationary environments.
Frequently Asked Questions (FAQ)
General Algorithm Concepts
What is the difference between exploration and exploitation in metaheuristics?
Exploration is the process of discovering diverse solutions in different regions of the search space to identify promising areas, while exploitation intensifies the search within these promising areas to refine solutions and accelerate convergence [28]. Maintaining the right balance is crucial, as excessive exploration slows convergence, while predominant exploitation leads to local optima [28].
How does the Raindrop Algorithm (RD) balance exploration and exploitation?
The Raindrop Algorithm comprises two distinct phases. During the exploration phase, it employs mechanisms like splash, diversion, and evaporation to enhance global search capabilities. In the exploitation phase, it simulates raindrop convergence and overflow behaviors to improve local search performance [29].
Are there hybrid strategies to improve the exploration-exploitation balance?
Yes, hybrid strategies combine global and local search methods. For example, the G-CLPSO strategy combines the global search characteristics of Comprehensive Learning Particle Swarm Optimization (CLPSO) with the exploitation capability of the Marquardt-Levenberg method, demonstrating superior performance in accuracy and convergence [30].
Implementation and Tuning
What does the convergence characteristic of the Raindrop Algorithm look like?
The Raindrop Algorithm demonstrates rapid convergence characteristics, typically achieving optimal solutions within 500 iterations while maintaining computational efficiency [29].
How do Competitive Swarm Optimizer (CSO) variants enhance performance?
Competitive Swarm Optimizer with Mutated Agents (CSO-MA) adds a mutation step to the standard CSO. It randomly chooses a loser particle, picks a variable, and changes its value to a boundary value. This increases solution diversity and helps prevent premature convergence to local optima [31].
Can you provide a visual representation of a hybrid optimization workflow?
The following diagram illustrates the workflow of a hybrid global-local optimization strategy, such as G-CLPSO, which combines stochastic global search with deterministic local exploitation:
Troubleshooting Common Experimental Issues
Algorithm Performance Problems
| Problem | Possible Causes | Solutions |
|---|---|---|
| Premature Convergence | Over-emphasis on exploitation, insufficient population diversity [28] | Increase exploration mechanisms (e.g., mutation rate in CSO-MA [31]), use hybrid strategies [30] |
| Slow Convergence | Excessive exploration, poor parameter tuning [28] | Balance phases (e.g., fine-tune social factor φ in CSO [31]), implement local search exploitation [30] |
| High Computational Cost | Large population size, complex fitness evaluation | Limit iterations (e.g., Raindrop Algorithm typically converges in <500 iterations [29]), use efficient sampling |
Implementation and Validation
| Problem | Possible Causes | Solutions |
|---|---|---|
| Poor Solution Quality | Inadequate balance between exploration and exploitation [28] | Validate on benchmarks (e.g., CEC-BC-2020 [29]), use statistical tests (e.g., Wilcoxon rank-sum [29]) |
| Parameter Sensitivity | Over-fitting to specific problems | Test on diverse functions (separable/non-separable, unimodal/multimodal [31] [30]) |
| Performance Inconsistency | Stochastic nature of algorithms | Conduct multiple independent runs, report statistical significance [29] |
Experimental Protocols and Methodologies
Benchmarking Algorithm Performance
Objective: Evaluate the performance of nature-inspired metaheuristics on standard test functions.
Procedure:
- Select Benchmark Functions: Choose a diverse set of 23 benchmark functions and CEC-BC-2020 benchmark suite [29]
- Configure Algorithms: Set population size, iteration limits, and algorithm-specific parameters
- Execute Multiple Runs: Perform independent runs to account for stochastic variations
- Collect Data: Record convergence curves, final solution quality, and computational time
- Statistical Analysis: Apply Wilcoxon rank-sum tests to validate statistical significance [29]
Expected Outcomes: Quantitative comparison of solution quality, convergence speed, and robustness across different problem types.
Engineering Application Validation
Objective: Validate algorithm performance on real-world engineering optimization problems.
Procedure:
- Problem Selection: Identify complex, nonlinear constrained optimization problems [29]
- Algorithm Implementation: Apply metaheuristics (e.g., Raindrop Algorithm) to problem domain
- Performance Metrics: Measure solution quality, computational efficiency, and improvement over baseline methods
- Comparative Analysis: Benchmark against conventional optimization approaches
Application Example: In robotic engineering, the Raindrop Algorithm achieved an 18.5% reduction in position estimation error and 7.1% improvement in overall filtering accuracy compared to conventional methods [29].
Quantitative Performance Data
Algorithm Convergence Characteristics
| Algorithm | Typical Convergence Iterations | Key Strengths | Benchmark Performance |
|---|---|---|---|
| Raindrop Algorithm (RD) | <500 iterations [29] | Rapid convergence, balanced phases | First-place in 76% of test cases; statistically superior in 94.55% of CEC-BC-2020 cases [29] |
| CSO-MA | Varies by dimension [31] | Mutation prevents local optima | Competitive on high-dimensional problems (up to 5000 dimensions) [31] |
| G-CLPSO | Faster than CLPSO [30] | Hybrid global-local search | Superior accuracy and convergence in non-separable functions [30] |
Engineering Application Results
| Application Domain | Algorithm | Performance Improvement |
|---|---|---|
| Robotic Engineering | Raindrop Algorithm | 18.5% reduction in position estimation error; 7.1% improvement in filtering accuracy [29] |
| Statistical Modeling | CSO-MA | Effective for maximum likelihood estimation, Rasch models, M-estimation [31] |
| Hydrological Modeling | G-CLPSO | Outperformed gradient-based and stochastic algorithms in inverse estimation [30] |
The Scientist's Toolkit: Research Reagent Solutions
Essential Algorithmic Components
| Research Reagent | Function in Optimization | Example Implementation |
|---|---|---|
| Exploration Mechanisms | Discover promising regions in search space | Splash, diversion, evaporation in Raindrop Algorithm [29] |
| Exploitation Mechanisms | Refine solutions in promising regions | Convergence, overflow in Raindrop Algorithm [29] |
| Hybridization Strategies | Combine global exploration with local exploitation | G-CLPSO: CLPSO + Marquardt-Levenberg method [30] |
| Mutation Operators | Maintain population diversity | CSO-MA boundary mutation [31] |
| Benchmark Suites | Validate algorithm performance | 23 benchmark functions, CEC-BC-2020 suite [29] |
Algorithm Phase Transition Logic
The following diagram illustrates the decision process for transitioning between exploration and exploitation phases in nature-inspired metaheuristics, crucial for maintaining balance throughout the optimization process:
Frequently Asked Questions
Q1: What does "premature convergence" mean in practice, and how can I detect it in my optimization runs? Premature convergence occurs when an algorithm becomes trapped in a local optimum, stalling the search for a globally superior solution. You can detect it by monitoring population diversity, which is the degree of dispersion of individuals in the search space [32]. A consistently low diversity value indicates that the population is too concentrated and likely stagnating [32]. Similarly, a lack of improvement in the fitness of the best solution over successive iterations is a key indicator.
Q2: My algorithm is not exploring the search space effectively. How can I encourage more exploration? To enhance exploration, you can:
- Implement an adaptive niching method that divides the population into subpopulations (niches) to maintain diversity and explore multiple regions of the fitness landscape simultaneously [32].
- Use a diversity-controlled mutation strategy that selects mutation operators favoring exploration when population diversity is low [32].
- Dynamically adjust the step-size parameter based on the current solution's fitness, allowing for larger jumps in the search space during the early stages of optimization [33].
Q3: How can I balance the trade-off between exploration and exploitation automatically? An effective method is to use a framework for Adaptive Strategy Management (ASM). This framework dynamically switches between different solution-generation strategies based on real-time performance feedback [34]. The core steps are:
- Filtering: Deciding which candidate solutions to consider.
- Switching: Choosing the most appropriate search strategy (e.g., exploration- or exploitation-focused).
- Updating: Refining the model and strategies based on new results [34]. Population diversity can serve as the primary metric for this trade-off, with high diversity triggering exploitative behaviors and low diversity triggering exploratory behaviors [32].
Q4: What is a practical way to handle parameters that are sensitive or difficult to set? A robust approach is to reduce the algorithm's dependence on pre-defined parameters. For example, you can employ a diversity-based niching method that is not sensitive to the choice of parameters, as it adaptively partitions the population based on the current distribution of individuals rather than a fixed radius [32]. Another strategy is to refine the algorithm's core equations to reduce the number of hyperparameters required [33].
Troubleshooting Guides
Problem: Algorithm Convergence to Local Optima Description: The optimizer repeatedly returns a suboptimal solution, failing to find the global best. Solution Steps:
- Integrate a Local Optima Processing Strategy: Employ a tabu archive to record previously discovered optima. When a subpopulation is identified as prematurely convergent (its diversity falls below a threshold for several iterations), reinitialize its individuals while using the archive to avoid re-exploring the same regions [32].
- Adopt a Dynamically Scaled Step-Size: Incorporate an adaptive method that adjusts the step-size parameter based on the current solution's fitness. This helps the algorithm escape local optima by taking larger steps when needed [33].
- Verify Strategy Switching: If using an Adaptive Strategy Management (ASM) framework, ensure the switching mechanism is guided by knowledge of the global best solution to help direct the search away from less promising areas [34].
Problem: Poor Balance Between Exploration and Exploitation Description: The algorithm either wanders randomly without converging or converges too quickly. Solution Steps:
- Monitor Population Diversity: Track diversity metrics throughout the search process. A high diversity value implies exploration, while a low value reflects exploitation [32].
- Implement Adaptive Mutation Selection: Design a mechanism that allows each subpopulation to select a mutation operator adaptively at each iteration. The choice should be based on factors like problem dimensionality and the subpopulation's current diversity, enabling a better balance [32].
- Apply a Filtering and Switching Framework: Use the ASM framework to systematically alternate between exploratory and exploitative strategies. Methods like "ASM-Close Global Best," which combine proximity filtering with global best knowledge, have demonstrated robust convergence and high-quality solutions [34].
Problem: High Computational Cost for Large-Scale Problems Description: The optimization process is too slow or computationally expensive, especially for very large-scale design problems. Solution Steps:
- Utilize an Adaptive Strategy Management Framework: The ASM framework is specifically designed to enhance the efficiency of computationally expensive processes by dynamically deciding which solutions to evaluate, thus reducing unnecessary computations [34].
- Employ a Surrogate Model with Active Learning: In an active learning loop, use a surrogate model (e.g., a machine learning model) to make predictions. Guide experiments or calculations by maximizing a utility function (like expected improvement) to prioritize the most informative data points, reducing the number of costly evaluations required [35].
Experimental Protocols for Cited Methods
1. Protocol for Implementing Adaptive Strategy Management (ASM) This protocol is based on the ASM framework for large-scale structural optimization [34].
- Objective: To dynamically switch between multiple solution-generation strategies to improve optimization efficiency.
- Core Components:
- Filtering: Decide which candidate solutions to evaluate. Methods can include proximity-based filtering to ensure feasibility and stability.
- Switching: Adaptively decide when to switch strategies based on real-time performance feedback. Switching can be guided by the current best or global best solutions.
- Updating: Continuously update the strategy performance models and the population of solutions.
- Methodology:
- Select a core optimizer (e.g., Chaos Game Optimization was used in the original study).
- Define a set of solution-generation strategies.
- At each iteration, execute the ASM cycle (Filtering → Switching → Updating).
- Evaluate new solutions and update the global best.
- Validation: Evaluate the performance on benchmark structural problems and compare against state-of-the-art optimizers using convergence speed and solution quality metrics.
2. Protocol for Diversity-Based Adaptive Differential Evolution (DADE) This protocol outlines the use of the DADE algorithm for multimodal optimization problems [32].
- Objective: To locate as many global optima as possible in a multimodal landscape.
- Core Components:
- Diversity-Based Niching: Adaptively divide the population into subpopulations (niches) using a modified diversity measurement to determine niche membership.
- Adaptive Mutation Selection: For each niche, adaptively choose a mutation operator based on problem dimensionality and the niche's current diversity.
- Local Optima Processing: Use a tabu archive (elite set and tabu regions) to reinitialize niches that show premature convergence.
- Methodology:
- Initialize the population and parameters.
- Loop until termination: a. Measure population diversity and perform niching. b. For each niche, select a mutation strategy and generate offspring. c. Identify stagnating niches and reinitialize them using the tabu archive. d. Evaluate new individuals and update the population.
- Validation: Test the algorithm on a suite of multimodal benchmark functions (e.g., from CEC2013) and compare its performance (number of optima found, convergence rate) against other state-of-the-art multimodal algorithms.
Research Reagent Solutions
The table below lists key algorithmic components and their functions in adaptive control methods.
| Research Reagent | Function & Purpose |
|---|---|
| Diversity Metric [32] | A measure of the dispersion of individuals in the population; used to quantify the balance between exploration and exploitation and trigger adaptive responses. |
| Niching Method [32] | A technique to subdivide the population into distinct subpopulations (niches), enabling the simultaneous discovery of multiple optimal solutions. |
| Tabu Archive [32] | A memory structure that stores previously discovered optima; used to help the algorithm escape local optima and avoid re-exploring the same regions. |
| Utility/Acquisition Function [35] | A function (e.g., Expected Improvement) used in Bayesian optimization to decide the next most promising data point to evaluate, guiding the search efficiently. |
| Surrogate Model [35] | A machine learning model that approximates a computationally expensive objective function; used to make predictions during the optimization process. |
| Strategy Switching Mechanism [34] | A component within the Adaptive Strategy Management framework that dynamically alternates between different search strategies based on performance feedback. |
| Control Systems Controller [36] | A decision-making algorithm that uses personalized dynamic models to enable daily, perpetual adaptation of intervention parameters, such as goal settings. |
Workflow and System Diagrams
The following diagram illustrates the high-level logical flow of an adaptive control process that balances exploration and exploitation, integrating concepts from the cited research.
Adaptive Control Process Flow
The diagram below provides a more detailed look at the Adaptive Strategy Management (ASM) framework, which is a specific method for dynamic strategy switching.
Adaptive Strategy Management (ASM) Cycle
Troubleshooting Guides
Guide 1: Resolving Premature Convergence in IFOX
Problem: The IFOX algorithm converges too quickly to suboptimal solutions during the molecular search space exploration, leading to poor property prediction accuracy.
Explanation: Premature convergence occurs when the algorithm's exploitation phase dominates too early, preventing a thorough exploration of the molecular configuration space. This is particularly problematic in materials science where optimal molecular configurations may exist in narrow regions of the search space [37].
Solution Steps:
- Implement Adaptive Step-Size Parameter: Modify the dynamic scaling of the step-size parameter based on current solution fitness, allowing the algorithm to automatically adjust between exploration and exploitation phases [38].
- Verify Parameter Settings: Ensure the removal of four redundant hyperparameters (C1, C2, a, Mint) has been properly implemented, as these often contribute to premature convergence in the original FOX algorithm [37] [38].
- Introduce Fitness-Based Adaptation: Implement the fitness-based adaptive method that scales exploration intensity according to solution quality, giving poorer solutions more exploration capability [38].
Validation: Monitor the population diversity metric throughout iterations. A gradual decrease rather than sharp drop indicates proper balance between exploration and exploitation.
Guide 2: Handling High-Dimensional Molecular Feature Spaces
Problem: Performance degradation when processing high-dimensional molecular descriptors and fingerprints in property prediction tasks.
Explanation: Molecular property prediction often involves processing numerous descriptors including topological, electronic, constitutional, and physicochemical features, leading to the "curse of dimensionality" [39].
Solution Steps:
- Apply Feature Selection Integration: Integrate ReliefF and Copula entropy during initialization phase to handle high-dimensional data, as demonstrated in improved grey wolf optimization variants [38].
- Implement Competitive Guidance Strategy: Utilize a competitive guidance strategy for flexible search in high-dimensional spaces [38].
- Employ Differential Evolution Mechanisms: Apply differential evolution-based methods to enhance leader positioning and avoid local optima in high-dimensional scenarios [38].
Validation: Compare solution quality using subsets of features; optimal performance should maintain consistency across different feature subsets.
Frequently Asked Questions
FAQ 1: How does IFOX specifically address the exploration-exploitation balance in molecular search spaces?
IFOX incorporates a novel fitness-based adaptive method that uses a dynamically scaled step-size parameter to autonomously balance exploration and exploitation based on the current solution's fitness value [38]. Unlike the original FOX algorithm which used a static 50/50 ratio between phases [37], IFOX adjusts this balance continuously throughout the optimization process. For molecular property prediction, this means the algorithm can spend more time exploring complex molecular configuration spaces early in the process, then gradually shift toward exploiting promising regions where optimal molecular structures are likely to be found [38].
FAQ 2: What molecular representations work best with IFOX for property prediction?
Based on current research, multiple molecular representations can be effectively utilized with IFOX:
Table: Molecular Representations for IFOX Integration
| Representation Type | Best Use Cases | IFOX Compatibility |
|---|---|---|
| Graph-based Representations (GNN) | Capturing topological relationships between atoms [39] [40] | High - aligns with IFOX's pattern recognition |
| Molecular Fingerprints (ECFP) | Structural similarity assessment and virtual screening [39] [40] | Medium - requires feature dimension optimization |
| SMILES Sequences | Sequential molecular data processing [39] | Low - less optimal for IFOX's operational mechanics |
| Multimodal Approaches | Complex property prediction combining multiple data types [39] | High - benefits from IFOX's adaptive capabilities |
The most effective approach often involves combining graph-based representations for intra-molecule information with fingerprint-based methods for inter-molecule relationships [40].
FAQ 3: What metrics should I use to evaluate IFOX performance in molecular optimization?
Table: Performance Metrics for IFOX in Molecular Property Prediction
| Metric Category | Specific Metrics | Target Values |
|---|---|---|
| Solution Quality | Mean Best Fitness, Standard Deviation [37] [38] | 40% improvement over baseline FOX [38] |
| Convergence Behavior | Convergence Speed, Success Rate [37] | 880 wins, 228 ties, 348 losses against 16 algorithms [38] |
| Statistical Significance | Friedman Test, Wilcoxon Signed-Rank Test [37] [38] | Average rank of 5.92 among 17 algorithms [38] |
| Computational Efficiency | Function Evaluations, Processing Time [37] | Equivalent or better than original FOX with improved results [38] |
Experimental Protocols
Protocol 1: Benchmark Testing for Algorithm Validation
Objective: Validate IFOX performance against standard benchmark functions before molecular application.
Methodology:
- Test Suite Configuration: Utilize 20 classical benchmark functions (10 unimodal, 10 multimodal) and 61 CEC functions from CEC 2017, 2019, 2021, and 2022 [37] [38].
- Parameter Settings: Implement the reduced parameter set excluding C1, C2, a, and Mint as described in IFOX specifications [38].
- Comparison Framework: Test against 16 state-of-the-art optimization algorithms including LSHADE and NRO [38].
- Statistical Analysis: Apply Friedman and Wilcoxon signed-rank tests for performance validation [37] [38].
Success Indicators: Achieving competitive performance with an average rank of 5.92 among 17 algorithms and significant improvement over basic FOX [38].
Protocol 2: Molecular Property Prediction Workflow
Objective: Implement IFOX for accurate molecular property prediction in drug discovery applications.
Methodology:
- Data Preparation: Convert molecular structures to graph representations and calculate molecular fingerprints (ECFP) [40].
- IFOX Configuration: Initialize with adaptive exploration-exploitation parameters specific to molecular space characteristics.
- Optimization Cycle: Execute IFOX with fitness function based on property prediction accuracy.
- Validation: Test optimized molecular representations on held-out test sets using standard MPP metrics [39] [40].
The Scientist's Toolkit
Table: Essential Research Reagents and Computational Tools
| Tool/Reagent | Function | Application in IFOX-MPP |
|---|---|---|
| Graph Neural Networks (GNN) | Atom-level molecular graph representation [40] | Extracts structural features for fitness evaluation |
| Extended Connectivity Fingerprints (ECFP) | Molecular structural representation [40] | Provides similarity metrics for inter-molecule relationships |
| Tanimoto Coefficient | Similarity calculation between molecular fingerprints [40] | Enables construction of molecular similarity graphs |
| Graph Structure Learning (GSL) | Learning relationships between molecules [40] | Enhances molecular embeddings using inter-molecule information |
| Two-Level Graph Framework | Combines atom-level and molecule-level representations [40] | Provides comprehensive molecular representation for IFOX optimization |
| Benchmark Molecular Datasets | Standardized performance evaluation [39] | Validates IFOX performance against established baselines |
Overcoming Common Pitfalls: Premature Convergence and Local Optima Traps
This technical support guide provides researchers and scientists with practical methodologies for diagnosing and addressing premature convergence and over-exploration in evolutionary and materials search algorithms.
Frequently Asked Questions (FAQs)
What are the primary indicators of premature convergence in an optimization run?
Premature convergence is typically indicated by a rapid loss of population diversity and the algorithm getting trapped in a suboptimal solution. Key signs include [41] [42]:
- Rapid Decrease in Population Diversity: A sharp, early drop in genotypic or phenotypic diversity within the population.
- Stagnation of Fitness: The best or average fitness of the population stops improving long before the search is complete, and this plateau persists for a significant number of generations [41].
- Population Homologization: The population of candidate solutions becomes overly similar, clustering tightly around a single point in the search space that does not represent a global optimum [43].
- Dominance of Suboptimal Traits: A particular set of genes (solution components) begins to dominate the population early in the search process, preventing the exploration of other promising regions [42].
How can I distinguish between healthy exploitation and problematic over-exploitation?
The distinction lies in the balance and timing of the search process. Exploitation is healthy when it refines promising solutions discovered during a prior phase of broad exploration. Over-exploitation, which leads to premature convergence, occurs when this refinement happens too soon, cutting off the discovery of potentially better regions. A process that converges to a stable point too early, often close to the starting point of the search and with a worse evaluation than the global optimum, is a hallmark of premature convergence [41]. Configuring an algorithm to be less greedy (e.g., via a lower selective pressure) can help overcome this issue [41].
What are the common algorithmic factors that contribute to premature convergence?
Several factors inherent to algorithm design can trigger premature convergence [42]:
- Excessive Selective Pressure: Overly favoring the most-fit individuals in the population rapidly reduces diversity [41] [42].
- Insufficient Genetic Variation: Weak mutation rates or ineffective crossover operators fail to introduce enough new genetic material to escape local optima [44] [42].
- Small Population Size: A small population provides a limited sampling of the search space, making it easier for a suboptimal solution to dominate.
My algorithm explores constantly but fails to find good solutions. Is this over-exploration?
Yes, this is a classic sign of over-exploration or a lack of exploitation. The algorithm is spending too many resources sampling new, random areas of the search space without effectively refining and converging on the promising solutions it has already found. This results in slow convergence and an inability to locate a precise, high-quality optimum, manifesting as a failure to improve the best-found solution over time [30].
Diagnostic Tables for Common Problems
Table 1: Signs of Premature Convergence vs. Over-Exploration
| Symptom | Premature Convergence | Over-Exploration |
|---|---|---|
| Population Diversity | Rapidly decreases and remains low [43] [42] | Remains high throughout the run |
| Fitness Progress | Stagnates early at a suboptimal level [41] | Improves slowly or erratically without stabilizing |
| Best Solution Quality | Suboptimal local optimum | Poor, fails to refine |
| Primary Cause | Excessive selective pressure; insufficient mutation [41] [42] | Weak selective pressure; excessive random search |
Table 2: Quantitative Metrics for Diagnosis
| Metric | How to Measure It | Interpretation |
|---|---|---|
| Genotypic Diversity | Mean Hamming distance between individuals in the population [43]. | A consistently low value suggests premature convergence. |
| Fitness Stagnation Counter | Number of generations without improvement in best fitness [41]. | A high and steadily increasing count indicates convergence. |
| Selection Pressure | Rate at which population fitness variance decreases [42]. | A very high rate suggests risk of premature convergence. |
Experimental Protocols for Diagnosis
Protocol 1: Tracking Population Diversity
Objective: To quantitatively monitor the loss of diversity during an evolutionary run. Materials: Optimization algorithm, population data logger, distance metric (e.g., Hamming distance for genotypes, Euclidean distance for parameters). Methodology:
- At each generation (or at regular intervals), calculate the average distance between all pairs of individuals in the population.
- Plot this average distance over the course of the run.
- A sharp, exponential decay in the diversity plot is a clear indicator of premature convergence [43].
Protocol 2: Fitness Landscape Ruggedness Analysis
Objective: To understand the multi-modal nature of the problem, which influences convergence behavior. Materials: Sampling algorithm (e.g., random walk), local search operator. Methodology:
- Perform a broad, random sampling of the search space.
- From multiple starting points, perform a simple hill-climbing search.
- If the local searches consistently converge to many different fitness peaks, the landscape is highly multi-modal (rugged). Algorithms prone to premature convergence will perform poorly on such landscapes [41].
Workflow Diagrams
Diagram: Diagnostic & Remedial Workflow
Research Reagent Solutions
Table 3: Algorithmic "Reagents" for Balancing Search
| Research "Reagent" (Technique) | Function | Primary Use Case |
|---|---|---|
| Niching Methods [43] | Preserves sub-populations around different optima to maintain diversity. | Preventing premature convergence on multi-modal fitness landscapes. |
| Island Models [43] | Isolates sub-populations to encourage independent exploration, with periodic migration. | Maintaining high-level diversity and exploring multiple search regions in parallel. |
| Adaptive Mutation Rates [42] | Dynamically adjusts mutation probability based on population diversity metrics. | Reactively injecting diversity when the population becomes too homogeneous. |
| Hybrid Global-Local Strategies [30] | Combines global explorative algorithms (e.g., PSO) with local exploitative methods (e.g., gradient descent). | Overcoming stagnation by adding directed local search after a broad global exploration. |
| Fitness Sharing [43] | Reduces the effective fitness of individuals in crowded regions of the search space. | Promoting exploration of less crowded, and potentially promising, regions. |
| Tabu Search [42] | Maintains a memory of recently visited solutions to avoid cycling back to them. | Forcing the algorithm to explore new regions by explicitly forbidding a return to recent areas. |
Frequently Asked Questions
1. What is the fundamental problem that escape mechanisms like random restarts aim to solve? Local search algorithms in optimization often get stuck in "local optima"—solutions that are better than all nearby ones but are not the best possible solution overall. Escape mechanisms provide strategies to break out of these local optima to continue the search for a global optimum [45] [46].
2. What is the difference between Stochastic Hill Climbing and Random-Restart Hill Climbing? Both are strategies to avoid local minima, but they operate differently. Stochastic Hill Climbing does not always take the best possible step; it sometimes chooses a random direction to maximize exploration. In contrast, Random-Restart Hill Climbing always takes the best step but runs the entire algorithm multiple times, each time starting from a new, random point in the search space [45].
3. How do these strategies relate to the balance of exploration and exploitation? Optimizing a search requires balancing two objectives: exploitation (using known information to get a high reward) and exploration (gathering new information for potential future gain). Random restarts and stochastic moves are methods to increase exploration, helping the algorithm to learn about the search space and avoid committing prematurely to a sub-optimal region [46] [15].
4. In a materials discovery context, what kind of "target subsets" might a researcher want to find? The goal is often not just a single optimal material, but a set of candidates that meet specific, complex criteria. Examples include finding all synthesis conditions that produce nanoparticles within a target size range for catalysis, identifying processing conditions for wide electrochemical stability windows in batteries, or mapping specific portions of a phase boundary [47].
5. Can these different escape mechanisms be combined? Yes, for best performance, strategies can be hybridized. For instance, one could combine the global search characteristic of a particle swarm algorithm with the local exploitation power of a gradient-based method, or use stochastic moves within a random-restart framework [45] [30].
Comparison of Escape Mechanism Strategies
The following table summarizes key characteristics of different strategies to escape local optima.
| Strategy | Core Principle | Key Advantage | Key Disadvantage | Typical Application Context |
|---|---|---|---|---|
| Random Restart | Runs a local search multiple times from new random initial points. [45] | Conceptually simple; can be highly parallelized. [45] | Can be computationally expensive; does not learn from previous restarts. [45] | Local search algorithms where the cost of a single run is low. [45] [46] |
| Stochastic Hill Climbing | Probabilistically accepts non-improving moves to explore more space. [45] | Avoids getting stuck on small local "hills" without a full restart. [45] | May wander or fail to converge if the probability of random moves is too high. [45] | Search spaces with many small, local optima. [45] |
| Hybrid Global-Local (e.g., G-CLPSO) | Combines a global search algorithm with a local exploitation method. [30] | Balances broad exploration with deep, precise exploitation for high accuracy. [30] | More complex to implement and tune than single-method approaches. [30] | Complex, high-dimensional optimization problems like hydrological model calibration. [30] |
| Bayesian Algorithm Execution (BAX) | Uses a probabilistic model and user-defined goals to guide data acquisition. [47] | Efficiently targets specific, complex experimental goals beyond simple optimization. [47] | Requires a statistical model and is more suited for sequential experimental design. [47] | Materials discovery with expensive experiments, aiming to find target property subsets. [47] |
Experimental Protocol: Implementing Random Restart for a Materials Search
This protocol outlines the steps to implement a Random-Restart Hill Climbing algorithm to search for a material with a target property, such as maximum hardness.
1. Problem Definition:
- Design Space (X): Define the discrete set of all possible synthesis or measurement conditions. For a material, this could be all possible combinations of chemical elements and their crystal structures. [47]
- Objective Function (f): Define the property to be optimized (e.g., hardness, magnetization). The goal is to find the point in the design space that maximizes this function. [12] [47]
2. Algorithm Initialization:
- Set the maximum number of restarts (
max_restarts). - Set the maximum number of iterations for each local search run (
max_iterations).
3. Execution Loop: The following workflow is executed for each restart until the budget is exhausted:
4. Local Search Run (e.g., Hill Climbing):
- Step 1: Generate a random initial candidate solution within the design space.
- Step 2: For a set number of iterations, evaluate the objective function for the current candidate and its immediate neighbors.
- Step 3: Move to the neighbor with the highest objective function value.
- Step 4: If no better neighbor exists, the local search has converged and terminates, returning the best solution found in that run.
5. Result: After all restarts are complete, the algorithm returns the best solution found across all local search runs. [45]
The Scientist's Toolkit: Key Research Reagent Solutions
The following table details essential computational and methodological "reagents" for implementing escape mechanisms in computational materials research.
| Item | Function in the Experiment |
|---|---|
| Discrete Design Space | A finite set of all possible synthesis conditions or material compositions to be searched. It defines the universe of candidates for the algorithm. [47] |
| Objective Function | A function that quantifies the performance or property of a candidate material (e.g., hardness, ionic conductivity). The algorithm's goal is to optimize this function. [47] |
| Probabilistic Surrogate Model | A statistical model (e.g., Gaussian Process) that predicts the objective function's value and uncertainty at any point in the design space, guiding intelligent exploration. [47] |
| Local Search Algorithm | A core optimizer (e.g., gradient-based method, hill climbing) that performs deep exploitation in a region to find a local optimum. [45] [30] |
| Acquisition Function | A utility function that uses the surrogate model to balance exploration and exploitation by scoring the potential value of evaluating each point in the design space. [47] |
Performance Metrics for Algorithm Evaluation
When comparing different strategies, researchers should track the following quantitative metrics to assess performance. These are especially relevant in a materials science context where experiments are costly. [47]
| Metric | Description | Importance for Materials Discovery |
|---|---|---|
| Convergence Accuracy | The value of the best-found solution (e.g., hardness of the discovered material). [30] | Directly measures the success in finding a high-performing material. |
| Convergence Speed | The number of experiments or iterations required to find a solution of a given quality. [30] [47] | Critical for reducing time and cost, especially with slow synthesis protocols. |
| Sample Efficiency | The number of experimental measurements required to achieve the experimental goal. [47] | Paramount when a single experiment (e.g., characterizing a new superconductor) is time-consuming or expensive. [47] |
In computational materials research and drug development, efficiently searching vast chemical spaces is paramount. This process hinges on a fundamental challenge: the exploration-exploitation trade-off. Exploration involves evaluating new, untested candidates to discover promising regions, while exploitation focuses on refining and optimizing the most successful candidates identified so far [5].
Effective Population Diversity Management is the key to balancing this trade-off. It ensures your search algorithm does not prematurely converge on a suboptimal solution (excessive exploitation) nor waste resources on unpromising areas of the search space (excessive exploration) [5]. This technical support center details advanced techniques, namely Adaptive Prioritized Experience Replay and Dynamic Evaporation Optimization, to help you master this balance in your experiments.
# FAQ & Troubleshooting Guide
## General Concepts and Configuration
Q1: What are the clear signs that my materials search algorithm has a poor exploration-exploitation balance?
You can diagnose this imbalance through several observable behaviors in your experimental runs:
- Signs of Excessive Exploitation (Premature Convergence): The algorithm quickly settles on a specific class of candidates early in the process. You will see a rapid decrease in the diversity of your candidate pool and a stagnation of performance improvements, likely missing superior materials [5].
- Signs of Excessive Exploration (Inefficient Search): The algorithm fails to show consistent improvement and seems to "jump" randomly between vastly different candidates without refining the best ones. This leads to high computational costs and slow convergence, as the system spends too much time in less promising regions of the search space [5].
Q2: How do the core techniques of Adaptive PER and Dynamic Evaporation fundamentally differ in their approach?
While both aim to manage population diversity, they are inspired by different principles and operate on distinct mechanisms:
- Adaptive Prioritized Experience Replay (PER) is a reinforcement learning technique. It treats past experiences (e.g., evaluated material candidates) unequally, prioritizing the replay of experiences from which the model can learn the most. This is typically measured using the Temporal-Difference error (TD-error), a indicator of how "surprising" or informative a past evaluation was [48] [49] [50]. Its core function is to improve data utilization efficiency.
- Dynamic Evaporation Optimization is a physically-inspired population-based metaheuristic. It mimics the evaporation behavior of water molecules on surfaces with different wettability. The "evaporation flux rate" of individuals (candidates) in the population controls the layout and interaction between them, dynamically shifting the search from a broad, exploratory "monolayer" phase to a focused, exploitative "droplet" phase [51]. Its core function is to directly manage population distribution and convergence.
## Technical Implementation and Debugging
Q3: My implementation of Prioritized Experience Replay is unstable. The learning performance oscillates or collapses. What is the most common cause and how can I fix it?
Instability in PER is frequently caused by stale priorities and the resulting bias in the learning updates.
- Root Cause: In standard PER, the priorities (TD-errors) for most experiences stored in the replay buffer are not updated in real-time. Only the priorities for the small batch of data currently being replayed are updated. This creates a growing discrepancy between the stored priorities and the real, current priorities, introducing bias into the agent's learning process [49].
- Solution: Implement a priority correction mechanism. One advanced method is Importance-PER (Imp-PER), which uses Importance Sampling to correct the update direction without the prohibitive cost of updating the entire buffer. It estimates the real sampling probabilities of the replayed data and uses an importance weight to correct the loss function, stabilizing training [49].
Q4: What are the critical hyperparameters for tuning Water Evaporation Optimization (WEO), and how do they affect the exploration-exploitation balance?
The behavior of WEO is controlled by evaporation probability parameters, which directly govern the trade-off.
- Monolayer Evaporation Probability (MEP): Controls the evaporation of individuals that are spread out (exploration phase). A higher probability encourages more exploration of the search space [51].
- Droplet Evaporation Probability (DEP): Controls the evaporation of individuals that have clustered together (exploitation phase). A higher probability helps the algorithm avoid local optima by breaking up clusters, while a lower probability allows for finer refinement [51].
- Adaptive Strategy: The algorithm dynamically shifts between these evaporation modes based on the perceived "wettability" of the search space, which represents the quality of solutions found. This provides a built-in mechanism for balancing the trade-off [51].
Q5: My agent isn't learning anything useful, even with PER. What basic checks should I perform first?
Before fine-tuning complex algorithms, establish a solid baseline with these steps [52] [53]:
- Validate your state representation: Ensure the agent has access to all the information (state) needed not only to choose an action but also to predict the resulting reward. The state must satisfy the Markov property [52].
- Establish performance baselines: Benchmark your RL agent against a random agent and a simple, hand-coded policy. This verifies that your environment and reward function are structured correctly and that the agent is capable of learning [52].
- Scale your inputs and rewards: Normalize state observations and rewards to a consistent range (e.g., [-1, 1]). Well-scaled data is critical for stable neural network training [52] [53].
- Start simple: Begin with a minimal version of your problem—a simple reward signal, small state/action space, and short episodes. Only add complexity once you confirm learning is occurring [52].
## Performance and Evaluation
Q6: What level of performance improvement can I realistically expect from implementing these advanced techniques?
Empirical studies, particularly in reinforcement learning, show that PER can yield significant gains in efficiency and performance. The table below summarizes typical improvements observed in benchmark environments [50].
Table 1: Quantitative Performance Improvements with Prioritized Experience Replay
| Metric | Uniform Sampling DQN | Prioritized Experience Replay (PER) |
|---|---|---|
| Median Normalized Score (Atari) | 48% (Baseline) | 106% - 128% |
| Mean Score Improvement | Baseline | ~2x - 3x |
| Data Efficiency | Baseline | ~40% of training frames to match baseline performance |
| Success Rate | Baseline | Significant improvement in success rate and cumulative reward [48] |
For WEO, testing on benchmark constrained functions and engineering problems has demonstrated that it is "highly competitive with other efficient well-known metaheuristics" [51].
# The Scientist's Toolkit: Research Reagent Solutions
Table 2: Essential Computational Components for Algorithm Experimentation
| Research Reagent (Component) | Function & Explanation |
|---|---|
| Experience Replay Buffer | A memory store that holds past experiences (state, action, reward, next state). It breaks temporal correlations in data and enables sample reuse [49]. |
| Priority Metric (TD-Error) | A value assigned to each experience in the replay buffer, signifying its potential learning value. The Temporal-Difference error measures the discrepancy between predicted and target Q-values [48] [50]. |
| Importance Sampling (IS) Weight | A correction factor applied during learning to counteract the bias introduced by non-uniform (prioritized) sampling from the replay buffer, ensuring convergence [49] [50]. |
| Sum-Tree Data Structure | A specialized data structure that allows for efficient sampling of experiences based on their priority, reducing the time complexity of sampling from O(N) to O(logN) [50]. |
| Evaporation Probability Parameters | In WEO, these parameters (Monolayer and Droplet) control the rate at of "evaporation" for individuals in the population, directly managing the shift from exploration to exploitation [51]. |
# Experimental Protocols & Data
## Protocol 1: Implementing Adaptive Prioritized Experience Replay
This protocol outlines the key steps for integrating PER into a Deep Q-Network (DQN) framework for a materials search simulation [48] [50].
- Initialization: Create an empty replay buffer
Bwith a fixed capacityN. - Interaction & Storage: For each simulation step, store the transition
(s, a, r, s')inB. Calculate its initial priorityp_i = |δ_i| + ε, whereδ_iis the TD-error andεis a small constant to ensure all samples can be visited. - Priority-Based Sampling: To update the network, sample a mini-batch of transitions with probability
P(i) = p_i^α / Σ_k p_k^α. The exponentαdetermines how much prioritization is used (0=uniform, 1=full prioritization). - Importance-Sampling Correction: Calculate the loss for each sampled transition
iand weight it byw_i = ( (1/N) * (1/P(i)) )^β. The factorβis annealed from a initial value to 1 to gradually correct for bias. - Priority Update: After the network update, recalculate the TD-errors for the transitions in the mini-batch and update their priorities
p_iin the bufferB.
## Protocol 2: Configuring Water Evaporation Optimization
This protocol describes the setup for applying WEO to a materials optimization problem [51].
- Parameter Initialization: Set the algorithm parameters:
nWM: Number of water molecules (population size).t_max: Maximum number of iterations.MEP_min,MEP_max: Range for Monolayer Evaporation Probability.DEP_min,DEP_max: Range for Droplet Evaporation Probability.
- Population Initialization: Generate an initial population of
nWMcandidates (water molecules) randomly within the search space. - Iterative Evaporation Process: Until
t_maxis reached:- Evaluation: Calculate the fitness (objective function) for each candidate.
- Evaporation Type Selection: Based on the surface "wettability" (a function of current fitness), decide whether the system is in a monolayer or droplet state.
- Candidate Update: Update the position of each candidate based on the selected evaporation probability (MEP or DEP), which controls whether they explore new areas or exploit known good regions.
- Parameter Adaptation: Dynamically adjust the evaporation probabilities based on the search progress.
Table 3: Hyperparameter Settings for Balancing Trade-Offs
| Algorithm | Hyperparameter | Typical Value / Range | Effect on Exploration (↑) / Exploitation (↑) |
|---|---|---|---|
| Prioritized Experience Replay | Priority Exponent (α) |
0.6 - 0.7 | Higher α increases focus on high-error samples (↑ Exploitation of knowledge). |
IS Exponent (β) |
Annealed from 0.4-0.5 to 1 | Lower initial β reduces correction, accepting more bias (↑ Exploitation). Final value of 1 ensures unbiased convergence. |
|
Constant (ε) |
10⁻⁶ to 10⁻² | Ensures minimum sampling probability, maintaining a base level of exploration. | |
| Water Evaporation Optimization | Monolayer Evap. Prob. (MEP) |
User-defined between min/max | A higher MEP encourages more Exploration. |
Droplet Evap. Prob. (DEP) |
User-defined between min/max | A higher DEP helps escape local optima, indirectly aiding Exploration. A lower DEP allows for Exploitation. |
# Workflow Visualization
## Adaptive PER Implementation Workflow
The following diagram illustrates the core loop of implementing and using Adaptive Prioritized Experience Replay.
## Exploration vs. Exploitation Dynamics
This diagram conceptualizes how the two techniques manage the balance between exploration and exploitation over the course of an experiment.
Troubleshooting Guides
Guide 1: Resolving Poor Model Convergence in Material Property Prediction
Problem: Your machine learning model for predicting material properties (e.g., bandgap, catalytic activity) fails to converge or shows erratic training loss.
Diagnosis Steps:
- Check the learning rate: This is the most common culprit. A learning rate that is too high causes the loss to diverge or oscillate; one that is too low leads to negligible updates and stagnant progress [54] [55].
- Inspect the loss curve: Look for patterns—a steep, sudden rise indicates a drastically high learning rate; a flat line suggests a learning rate that is too low or vanishing gradients [55].
- Verify data preprocessing: Ensure that input features (e.g., atomic descriptors, composition vectors) are normalized. Unnormalized data can destabilize gradient-based optimization [55].
- Review model capacity: If the model architecture (e.g., graph neural network for molecules) is too complex for the amount of available data, it may overfit and fail to learn generalizable patterns [56].
Solutions:
- Systematically tune the learning rate: Perform a coarse-to-fine search on a logarithmic scale, for example, testing values like (10^{-3}, 10^{-4}, 10^{-5} ) [57] [54]. Use a learning rate schedule to decay it over time [57].
- Adjust batch size and retune: When you change the batch size, you must re-tune the learning rate and regularization hyperparameters. The largest batch size your hardware can support is often a good starting point for minimizing training time [55].
- Apply gradient clipping: This can stabilize training by preventing exploding gradients, especially in deep networks or when dealing with noisy data from high-throughput material simulations [55].
Guide 2: Optimizing Exploration vs. Exploitation in Materials Search Algorithms
Problem: Your Bayesian optimization routine for discovering new materials (e.g., stable crystal structures, efficient drug molecules) is either stuck in a local optimum or inefficiently exploring the vast chemical space.
Diagnosis Steps:
- Analyze the acquisition function: Determine if its behavior is overly exploitative (focusing only on the current best area) or overly exploratory (wasting evaluations on unpromising regions) [58] [59].
- Check the kernel of the Gaussian Process (GP): The kernel choice and its length-scale parameters dictate the smoothness and shape of the surrogate model, which directly impacts the balance [58].
- Evaluate the optimization history: Plot the selected candidate materials over time to see if they are clustered in one small region or spread widely across the parameter space [58].
Solutions:
- Tune the acquisition function's parameters: For the Upper Confidence Bound (UCB) function, adjust the
kappaparameter. A higherkappaencourages more exploration [58]. - Dynamic parameter adjustment: Implement a schedule to start with a high
kappa(exploration) and gradually reduce it (exploitation) as the optimization progresses [59]. - Incorporate domain knowledge: Use prior knowledge about material science to constrain the search space. For instance, you can define boundaries for plausible lattice constants or atomic radii to reduce the ineffective exploration space [56] [60].
Guide 3: Managing Computational Budget in Large-Scale Hyperparameter Optimization
Problem: Hyperparameter optimization for a large-scale molecular dynamics model (e.g., using a Machine Learning Interatomic Potential - MLIP) is prohibitively slow and computationally expensive.
Diagnosis Steps:
- Identify the bottleneck: Profile your code to see if the time is spent on model training, model inference, or the HPO algorithm itself [60].
- Assess the search space dimensionality: A search space with too many hyperparameters (e.g., simultaneously tuning network depth, width, learning rate, and regularization) will suffer from the curse of dimensionality [57] [61].
- Evaluate the HPO method: Grid search becomes infeasible in high-dimensional spaces, while random search, though better, may still be inefficient [57] [61].
Solutions:
- Adopt a staged search strategy:
- Prioritize important hyperparameters: Use techniques like functional Analysis of Variance (fANOVA) to identify which hyperparameters most significantly impact your model's performance. Focus your computational resources on tuning these key parameters [59].
- Leverage hardware acceleration: For tasks like geometry relaxation of thousands of candidate materials, use batched processing on GPUs. Tools like the NVIDIA Batched Geometry Relaxation NIM can provide speedups of 100x or more compared to sequential CPU-based processing [60].
Frequently Asked Questions (FAQs)
Q1: In the context of materials science, which hyperparameters should I prioritize tuning first?
The learning rate is almost always the most critical hyperparameter and should be tuned first [54] [55]. Following that, focus on optimization-specific parameters (like momentum) and regularization parameters (like L2 penalty or dropout strength) [57]. For AI-driven materials discovery pipelines that involve Bayesian optimization, the acquisition function's parameters (e.g., kappa in UCB) that control exploration-exploitation are also high-priority tuning targets [58] [59].
Q2: Why should I use a logarithmic scale to search hyperparameters like the learning rate? Many hyperparameters, such as the learning rate and regularization strength, have a multiplicative effect on the training dynamics [57]. Searching on a linear scale (e.g., [0.1, 0.2, ..., 1.0]) would waste resources on a single order of magnitude. A logarithmic scale (e.g., [0.1, 0.01, 0.001]) allows you to efficiently explore several orders of magnitude, which is where the optimal value is likely to reside [57] [54].
Q3: When should I use Bayesian Optimization over Grid Search or Random Search? Bayesian Optimization (BO) is particularly superior in scenarios characterized by [58] [61]:
- High-dimensional search spaces: Where grid search becomes computationally intractable.
- Expensive function evaluations: When each model training (e.g., a large-scale DFT calculation or molecular dynamics simulation) takes hours or days.
- Limited evaluation budget: BO intelligently models the objective function and balances exploration with exploitation, often finding a good solution in far fewer iterations than random search.
Q4: My model's performance is highly sensitive to small changes in a hyperparameter. How can I make it more robust? This is often a sign of overfitting to the validation set or an overly complex model. Solutions include [57] [55]:
- Increase the size of your validation set to make performance estimates more reliable.
- Add or strengthen regularization (e.g., L2 regularization, dropout, early stopping).
- Collect more training data or use data augmentation techniques specific to your domain (e.g., symmetry operations for crystal structures).
- Reduce model complexity (e.g., reduce the number of layers or units in a neural network).
Q5: How can I adapt hyperparameter optimization for continual learning scenarios in dynamic material discovery platforms? In continual learning, where data from new experiments or simulations arrives sequentially, re-tuning all hyperparameters from scratch for each task is inefficient. An adaptive HPO approach is recommended [59]:
- Use an initial set of tasks to identify the most important hyperparameters using fANOVA.
- For subsequent tasks, perform warm-start HPO by focusing the search only on these important hyperparameters, starting from the best configuration of the previous task. This drastically reduces the search space and computational cost while maintaining robust performance across a sequence of tasks [59].
Experimental Protocols & Data
Protocol 1: Coarse-to-Fine Hyperparameter Search
This methodology is designed for efficiently tuning expensive models, such as those used in molecular property prediction [57].
- Define a broad search space for key hyperparameters (e.g., learning rate from (10^{-6}) to (10^{-1}), batch size from 32 to 1024).
- Perform a random search with 20-50 trials within this coarse space. Train each model for a reduced number of epochs (e.g., 1-5 epochs) to quickly identify promising regions.
- Analyze results and select the top 10% of configurations based on validation performance.
- Define a refined, narrower search space around the values of these best-performing configurations.
- Perform a second search (random or Bayesian) within this refined space, now training models for the full number of epochs to determine the final optimal hyperparameters.
Protocol 2: Bayesian Optimization for Materials Discovery
This protocol outlines using BO to optimize an acquisition function for discovering new materials with target properties [58].
- Define the search space: This includes the composition, structure, or processing parameters of the material (e.g., ratios of chemical elements, annealing temperature).
- Choose a surrogate model: A Gaussian Process (GP) is a common choice to model the unknown function mapping material parameters to a property of interest.
- Select an acquisition function: The Upper Confidence Bound (UCB) is recommended for its explicit exploration-exploitation trade-off controlled by the
kappaparameter [58]. - Initialization: Run a small number of random experiments to build an initial dataset.
- Iterate until budget is exhausted: a. Fit the GP surrogate model to all available data. b. Find the material parameters that maximize the acquisition function. c. Evaluate the candidate (via simulation or experiment) to get its true property value. d. Add the new (parameters, value) pair to the dataset.
The following tables summarize key quantitative findings from the search results.
Table 1: Comparison of Hyperparameter Optimization Methods [58] [61]
| Method | Principle | Iteration Efficiency | Resource Consumption | Best For |
|---|---|---|---|---|
| Grid Search | Exhaustive combination trial | ★☆☆☆☆ | Very High | Low-dimensional spaces (≤3 parameters) |
| Random Search | Random parameter sampling | ★★☆☆☆ | High | Quick, coarse-grained exploration |
| Bayesian Optimization | Probability model-guided sampling | ★★★★★ | Medium | High-dimensional spaces / expensive evaluations |
Table 2: Acceleration of Material Screening via Batched GPU Processing [60]
| System Type | Batched Geometry Relaxation NIM | Batch Size | Total Time | Speedup vs. CPU |
|---|---|---|---|---|
| Inorganic Crystals (2,048 systems) | Off | 1 | ~874 sec | 1x (baseline) |
| Inorganic Crystals (2,048 systems) | On | 128 | ~9 sec | ~100x |
| Organic Molecules (851 systems) | Off | 1 | ~678 sec | 1x (baseline) |
| Organic Molecules (851 systems) | On | 64 | ~0.9 sec | ~800x |
Workflow Visualizations
Bayesian Optimization for Materials Discovery
Adaptive Hyperparameter Optimization for Continual Learning
The Scientist's Toolkit: Essential Research Reagents & Solutions
Table 3: Key Tools for AI-Driven Material Discovery and HPO
| Tool / Solution | Function / Purpose | Context of Use |
|---|---|---|
| Density Functional Theory (DFT) | High-accuracy quantum mechanical calculation of material properties from first principles. | Generating training data and validating predictions from machine learning models [56] [60]. |
| Machine Learning Interatomic Potentials (MLIPs) | AI-based force fields that approximate DFT accuracy at a fraction of the computational cost. | Enabling large-scale (millions of atoms) and long-time-scale molecular dynamics simulations for material screening [60]. |
Bayesian Optimization Libraries (e.g., bayesian-optimization) |
Provide algorithms to efficiently optimize black-box functions, balancing exploration and exploitation. | Tuning model hyperparameters or guiding the discovery of new materials with target properties [58]. |
| fANOVA (functional ANOVA) | A statistical technique to quantify the importance of each hyperparameter and their interactions. | Analyzing HPO results to reduce search space dimensionality and focus tuning on the most impactful parameters [59]. |
| Batched Geometry Relaxation NIM (NVIDIA) | A GPU-accelerated microservice that performs thousands of geometry optimizations in parallel. | High-throughput screening of material stability by rapidly minimizing the energy of candidate structures [60]. |
| Symbolic Regression (e.g., PSRN) | Discovers interpretable mathematical expressions (physical laws) from observed data. | Deriving compact, human-understandable formulas that describe material behavior from complex simulation data [62]. |
Benchmarking and Validation: Ensuring Algorithmic Robustness in Scientific Discovery
Frequently Asked Questions
Q1: What are benchmark functions, and why are they crucial for validating materials search algorithms?
Benchmark functions are mathematical functions used to create a controlled, repeatable environment for evaluating and comparing the performance of optimization algorithms [63]. For materials search algorithms, which must balance exploration (searching new areas of the search space) and exploitation (refining known good solutions), these functions are essential [5]. They provide a standardized way to assess whether an algorithm can efficiently find optimal solutions without getting trapped in sub-optimal regions. Standardized test suites, like those from the IEEE Congress on Evolutionary Computation (CEC), offer a diverse set of challenges—from unimodal to highly complex composite functions—ensuring a algorithm's robustness and scalability are thoroughly tested before application to real-world, resource-intensive materials discovery problems [63] [64].
Q2: My algorithm performs well on simple tests but fails on CEC benchmarks. What is the likely cause?
This is a classic symptom of an algorithm that is over-exploiting and lacks sufficient exploration mechanisms. Simple test functions often have a single optimum (unimodal) or are separable, whereas modern CEC benchmarks are designed with real-world complexities in mind [63] [64].
- Non-separability and Rotation: CEC suites often apply rotation and shift operations to variables. This makes the problem non-separable, meaning variables interact with each other, and the global optimum is not trivially located. An algorithm that struggles with this may be unable to navigate the resulting complex, correlated landscapes [63] [64].
- Multi-modality: Functions like Rastrigin or Schwefel have many local optima. An algorithm that converges quickly is likely getting stuck in one of these, indicating a failure in exploration to escape local traps [63].
- Hybrid and Composition Functions: CEC benchmarks often combine different basic functions for different variables or regions of the search space. This creates a complex fitness landscape that requires an algorithm to dynamically switch between exploration and exploitation strategies [63] [64].
Q3: How do I choose the right performance metric? My results change when I use a different one.
The choice of performance metric is critical and should align with your primary goal. Using an inappropriate metric can lead to misleading conclusions about an algorithm's effectiveness [65]. The table below summarizes common metrics and their pitfalls.
| Metric | Best Used For | Common Pitfalls |
|---|---|---|
| Best-Found Fitness [65] | Applications where solution quality within a fixed time/budget is the primary concern. | May reward algorithms that find good-but-suboptimal solutions quickly but then stop improving. |
| Optimization Time [65] | Scenarios where the time to find the final, optimal solution is the most critical factor. | Can require prohibitively long runtimes to be measured accurately; may penalize algorithms that find good solutions early [65]. |
| Mean/Average Performance | Getting a general sense of typical algorithm performance across multiple runs. | Can be skewed by a few very poor or very good runs, hiding inconsistencies. |
| Statistical Tests (e.g., Wilcoxon, Friedman) [63] [64] | Rigorously comparing the performance of multiple algorithms across a benchmark suite to establish a statistically significant ranking. | Requires multiple independent runs (e.g., 30+); misuse or incorrect assumptions can lead to invalid conclusions [66]. |
Q4: What is a common statistical pitfall when comparing my algorithm to others?
A major pitfall is the multiple comparisons problem [67]. If you run many statistical tests (e.g., comparing your algorithm against several others on numerous benchmark functions), the chance of finding a statistically significant difference just by random chance (a false positive) increases dramatically. To avoid this, you must use post-hoc corrections that adjust significance levels, such as Holm's procedure [67].
Q5: How can I design my experiment to properly balance exploration and exploitation?
A well-designed experiment explicitly measures the balance between these two phases. The following workflow provides a structured methodology for setting up and analyzing your validation experiments.
Experimental Protocols for Validation
Protocol 1: Comprehensive Benchmark Evaluation using CEC Suites
This protocol outlines how to use CEC benchmark suites to stress-test your algorithm's core capabilities.
- Benchmark Selection: Select a recent CEC test suite (e.g., CEC 2021 or 2022). These suites typically include a mix of unimodal, multimodal, hybrid, and composition functions [64] [68].
- Parameter Initialization:
- Problem Dimension (D): Start with a moderate dimension (e.g., 30D) and scale up to test scalability.
- Search Space: Adhere to the bounds defined for each function in the test suite documentation.
- Algorithm Parameters: Set your algorithm's parameters (e.g., population size, mutation rates) to their default or baseline values.
- Stopping Criterion: Use a maximum number of function evaluations (e.g., 10,000 * D) to ensure fair comparison.
- Execution: Perform a minimum of 30 independent runs for each function-algorithm combination to account for stochasticity [63].
- Data Collection: For each run, record the best-found solution, the convergence curve (fitness over time), and the final computation time.
Protocol 2: Quantifying Exploration vs. Exploitation Behavior
This protocol provides a methodology to measure how an algorithm balances its search efforts, a critical aspect for dynamic materials search landscapes [15].
- Definition: For each generation or iteration of your algorithm, classify each solution update as either:
- Exploration: Moving to a solution that is significantly different from the current best (e.g., a large Hamming or Euclidean distance).
- Exploitation: Moving to a solution in the immediate neighborhood of the current best.
- Calculation: Count the number of exploratory (
D_explore) and exploitative (D_exploit) moves in an iteration. - Metric: Calculate the percentage of exploration and exploitation for that iteration as follows [63]:
% Exploration = (D_explore / (D_explore + D_exploit)) * 100% Exploitation = (D_exploit / (D_explore + D_exploit)) * 100
- Analysis: Plot these percentages over the course of a run. A well-balanced algorithm might show high exploration early on, with a gradual shift towards exploitation as it converges. The table below shows an example from a study on the Whale Optimization Algorithm (WOA) [63].
| Algorithm | Average Exploration % | Average Exploitation % |
|---|---|---|
| WOA (on traditional benchmarks) | 51.07% | 48.93% |
| Your Algorithm (to be filled) |
The Scientist's Toolkit: Research Reagents & Essential Materials
This table lists key "research reagents"—the benchmark functions and software tools—essential for building a robust validation framework.
| Item | Function / Purpose | Example in Context |
|---|---|---|
| Unimodal Functions | Test exploitation and convergence speed. Have a single global optimum. | Sphere Function: Validate an algorithm's ability to efficiently refine a solution and converge [63]. |
| Multimodal Functions | Test exploration and ability to escape local optima. Have multiple optima. | Rastrigin Function: Evaluate if the algorithm can navigate a "bumpy" landscape full of deceptive local solutions [63]. |
| Hybrid/Composite Functions | Test adaptive behavior on complex, real-world-like landscapes. Combine multiple basic functions. | CEC 2021/2022 Problems: Assess if the algorithm can dynamically switch strategies for different regions of the search space [64] [68]. |
| Shift & Rotation Operators | Remove algorithm bias and increase problem difficulty. Prevent trivial solutions by moving and rotating the function's optimum. | A rotated Rastrigin function is much harder to solve than the original, testing an algorithm's resilience to variable interactions [63] [64]. |
| Statistical Analysis Toolkit | Provide rigorous, unbiased comparison of algorithm performance. | Wilcoxon Signed-Rank Test & Friedman Test: Used to determine if performance differences between algorithms are statistically significant [63] [64]. |
Frequently Asked Questions (FAQs)
Q1: My optimization process consistently converges to local optima rather than the global solution. How can I improve the exploration capability of my algorithm?
The tendency to converge prematurely is often due to an imbalance between exploration and exploitation. The Improved FOX (IFOX) algorithm addresses this by introducing a fitness-based adaptive mechanism that dynamically scales the step-size parameter. This allows the algorithm to spend more time exploring the search space when the current solution's fitness is poor and switch to exploitation as it improves [37] [69]. For existing algorithms like PSO, you can modify the inertia weight (w) to decrease non-linearly over iterations, encouraging initial exploration (|A|>1 in GWO) followed by later exploitation (|A|<1 in GWO) [70] [71].
Q2: I am overwhelmed by the number of hyperparameters I need to tune for my optimization experiments. Are there algorithms with simplified parameter settings?
Yes, the IFOX algorithm was specifically designed to reduce this burden. It removes four hyperparameters (C1, C2, a, and Mint) present in the original FOX algorithm, thereby simplifying the setup process and making the algorithm more accessible and easier to implement [37] [69]. In contrast, while powerful, algorithms like PSO and GWO require careful tuning of parameters such as cognitive and social coefficients (c1, c2), inertia weight (w), and the coefficient vector a [70] [71] [72].
Q3: How can I rigorously and fairly evaluate the performance of a new optimization algorithm against established ones?
A comprehensive evaluation should involve three key components:
- Classical Benchmark Functions: Use a suite of standard functions, including unimodal (e.g., Sphere) to test convergence speed and multimodal (e.g., Rastrigin) to test the ability to avoid local optima [37] [69].
- CEC Benchmark Test Functions: Utilize the latest sets from the Congress on Evolutionary Computation (e.g., CEC 2017, 2019, 2021, 2022), which present more complex, real-world-like challenges [37].
- Real-World Engineering Problems: Test on constrained design problems such as Pressure Vessel Design (PVD) and Economic Load Dispatch (ELD) to demonstrate practical applicability [69] [73]. Performance should be compared using quantitative metrics (mean error, convergence speed) and non-parametric statistical tests like the Friedman test and Wilcoxon signed-rank test to confirm significance [37].
Q4: What is the fundamental difference between "exploration" and "exploitation" in the context of these algorithms?
- Exploration refers to the algorithm's ability to search broadly across different regions of the search space, gathering global information. It helps avoid premature convergence to local optima. In GWO, this is encouraged when
|A| > 1; in PSO, it's influenced by a higher inertia weight and the cognitive component [70] [71] [15]. - Exploitation is the process of refining a good solution found in a specific region, conducting an intensive local search. In GWO, this occurs when
|A| < 1; in PSO, it's driven by the social component and a lower inertia weight [70] [71] [15]. An optimal algorithm maintains a effective balance between these two competing objectives throughout the optimization process [30].
Experimental Protocols & Methodologies
Standardized Performance Evaluation Protocol
This protocol outlines the steps to fairly compare the performance of different optimization algorithms, as used in the evaluation of the IFOX algorithm [37].
- Objective: To quantitatively assess and compare the performance of optimization algorithms on a diverse set of test problems.
- Materials:
- Computing environment with MATLAB/Python.
- Implementation of algorithms to be tested (e.g., IFOX, LSHADE, GWO, PSO).
- Suite of benchmark functions.
- Procedure:
- Algorithm Setup: Initialize all algorithms with their respective recommended parameters. For example, set population size and maximum iterations consistently across all tests.
- Run Experiments: Execute each algorithm on each benchmark function for a predetermined number of independent runs (e.g., 30 runs) to account for stochastic variations.
- Data Collection: For each run, record the best solution found, the convergence history (fitness vs. iteration), and the computational time.
- Performance Calculation: Calculate the mean and standard deviation of the final solution quality across all runs for each algorithm-function pair.
- Statistical Testing: Perform non-parametric statistical tests (e.g., Friedman test for average ranking, Wilcoxon signed-rank test for pairwise comparisons) to determine if performance differences are statistically significant.
Workflow for Algorithm Performance Comparison
The following diagram illustrates the logical workflow for conducting a comparative analysis of optimization algorithms.
Performance Data & Analysis
Quantitative Performance Comparison of Algorithms
Table 1: Summary of algorithm performance across benchmark functions and real-world problems, based on data from Jumaah et al. (2025) [37].
| Algorithm | Key Inspiration/Method | Reported Performance (vs. IFOX) | Key Strength | Hyperparameter Count |
|---|---|---|---|---|
| IFOX | Adaptive step-size based on fitness [37] [69] | Baseline (880 wins, 228 ties, 348 losses) [37] | Balanced performance, fewer parameters [37] | Reduced (4 params removed from FOX) [37] |
| FOX | Foraging behavior of foxes [69] | 40% worse overall performance [37] | Simple foundation | Standard (more than IFOX) [37] |
| LSHADE | Success-history based parameter adaptation [74] | Competitive (IFOX avg. rank 5.92/17) [37] | Effective on complex functions [37] | Standard (with memory usage) [74] |
| GWO | Social hierarchy of grey wolves [70] | Outperformed by IFOX [37] | Simple concept, easy implementation [70] | Low [70] |
| PSO | Social behavior of bird flocking [71] | Outperformed by IFOX [37] | Fast convergence, simple logic [71] [72] | Standard (w, c1, c2) [71] |
| NRO | Nuclear fission & fusion phases [69] | Competitive (IFOX avg. rank 5.92/17) [37] | Strong global search capability [69] | Standard [69] |
Researcher's Toolkit: Essential Experimental Components
Table 2: Key "research reagents" and materials for conducting optimization experiments.
| Item / Concept | Function / Role in the Experiment | Example Instances |
|---|---|---|
| Benchmark Functions | Standardized test problems to evaluate algorithm performance on known landscapes. | Classical (Sphere, Rastrigin), CEC suites (CEC2017, CEC2022) [37] [69]. |
| Real-World Problems (RWPs) | Validate algorithm performance on practical, constrained engineering challenges. | Pressure Vessel Design (PVD), Economic Load Dispatch (ELD) [37] [69] [73]. |
| Performance Metrics | Quantitative measures to compare algorithm effectiveness and efficiency. | Best solution found, convergence speed, statistical test p-values [37]. |
| Statistical Test Suite | To determine the statistical significance of observed performance differences. | Friedman test (average ranking), Wilcoxon signed-rank test (pairwise comparison) [37]. |
| Population Topology | Defines the information flow and social structure between agents in a swarm. | Global topology (PSO), Ring topology (PSO), Social hierarchy (GWO) [70] [71]. |
Algorithm Workflows and Relationships
Simplified Workflow of the IFOX Algorithm
The diagram below outlines the core adaptive process of the Improved FOX algorithm.
Comparative Operator Behavior in GWO and PSO
This diagram contrasts the core position-updating mechanisms of two widely-used algorithms, GWO and PSO.
Frequently Asked Questions
Q1: When should I use the Friedman test versus the Wilcoxon signed-rank test?
The Friedman test is used when you want to compare three or more related groups or repeated measures. For example, you would use it to test if there is a difference in the performance of multiple algorithms across several different datasets, where the measurements are taken from the same subjects or under the same conditions [75] [76].
The Wilcoxon signed-rank test is specifically for comparing two related groups or paired samples. It is the non-parametric alternative to the paired t-test and is more powerful than the simpler sign test because it considers the magnitude of the differences between pairs, not just the direction [77] [78].
The table below summarizes the key differences:
| Feature | Wilcoxon Signed-Rank Test | Friedman Test |
|---|---|---|
| Number of Groups | Two related groups [78] | Three or more related groups [75] [76] |
| Common Use Case | Paired measurements (e.g., pre-test vs. post-test) [77] | Repeated measures (e.g., comparing >2 algorithms across multiple datasets) [75] |
| Non-parametric Alternative to | Paired t-test [78] | Repeated measures ANOVA [75] [76] |
Q2: My Friedman test is not significant, but my follow-up Wilcoxon tests show significant pairs. How is this possible?
This situation can and does occur. The Friedman test is an omnibus test that checks if there are any significant differences among all the groups you are comparing. It is possible for this overall test to not be significant, while direct, pairwise comparisons (like the Wilcoxon test) between two specific groups are significant [79].
This often happens when you have not corrected for multiple comparisons. When you perform multiple Wilcoxon tests (e.g., comparing Algorithm A vs. B, A vs. C, and B vs. C), you increase the chance of a false positive. To account for this, you should adjust your significance level using a method like the Bonferroni correction [75] [79]. For example, if your original significance level was 0.05 and you are making 3 pairwise comparisons, you would use a new significance level of 0.05/3 ≈ 0.0167 for each Wilcoxon test [75].
Q3: What are the key assumptions of the Wilcoxon signed-rank test?
The primary assumption is that the distribution of the differences between the two paired samples is symmetric [77]. This is a stronger assumption than the sign test, which only requires that the differences are independent. If you cannot assume symmetry, the sign test might be a more appropriate choice.
Troubleshooting Guide
Problem 1: Choosing the wrong test for multiple algorithm comparisons.
- Symptoms: You have performance data for four different search algorithms tested on the same 10 material datasets. You run multiple separate Wilcoxon tests to compare them all and struggle to interpret the results.
- Diagnosis: Using a test designed for two groups on a multiple-group problem. This leads to the multiple comparisons issue and an increased risk of Type I error (false positives).
- Solution: Use the Friedman test for the initial omnibus test. If the Friedman test is significant, you can then perform post-hoc analysis with pairwise Wilcoxon signed-rank tests, making sure to apply a correction for multiple comparisons like the Bonferroni correction [75] [79].
Problem 2: The Friedman test lacks power.
- Symptoms: You feel there should be a difference between your groups, but the Friedman test returns a non-significant p-value.
- Diagnosis: The Friedman test can sometimes have lower statistical power, especially with small sample sizes.
- Solution:
- Ensure your data is properly ranked within each block (e.g., within each dataset, you rank the algorithms from best to worst performance) [75] [76].
- If possible, increase your sample size (the number of blocks, e.g., datasets).
- Double-check that the Friedman test is the correct test for your data structure and that you have not violated its assumptions.
The following workflow diagram can help you navigate these decisions in the context of balancing exploration and exploitation in your research:
Decision Workflow for Non-Parametric Tests
Experimental Protocols
Protocol 1: Executing the Wilcoxon Signed-Rank Test
This test is ideal for a direct, powerful comparison of two related search strategies.
- Formulate Hypotheses: State your null hypothesis (H₀: the median difference between paired observations is zero) and alternative hypothesis (H₁: the median difference is not zero) [77].
- Compute Differences: For each paired data point (e.g., performance of Algorithm A vs. Algorithm B on the same dataset), calculate the difference [77].
- Rank the Differences: Rank the absolute values of these differences from smallest to largest, ignoring the sign. Remember the sign of each difference [77].
- Sum the Ranks: Calculate the sum of the ranks for the positive differences (W⁺) and the sum of the ranks for the negative differences (W⁻) [77].
- Determine Test Statistic: The test statistic, W, is the smaller of the two sums (W⁺ and W⁻) [77].
- Make a Decision: Compare your test statistic W to a critical value from a Wilcoxon table. If W is less than or equal to the critical value, you can reject the null hypothesis [77].
Protocol 2: Executing the Friedman Test
Use this protocol to screen multiple candidate materials or algorithms efficiently.
- Formulate Hypotheses: H₀: All algorithms have the same performance distribution. H₁: At least two algorithms differ in their performance distribution [75].
- Rank Data Within Blocks: In each row or "block" (e.g., each individual dataset), rank the values of the different algorithms from 1 (smallest) to k (largest). If there are ties, assign the average rank [75] [76].
- Calculate Sum of Ranks: For each algorithm (column), sum up all its ranks across all blocks. This gives you Rⱼ for each algorithm [75].
- Compute Test Statistic: Use the Friedman formula: Fᵣ = [12 / (nk(k+1))] * ΣRⱼ² - 3n(k+1) where n is the number of blocks, and k is the number of algorithms [75].
- Make a Decision: Compare the calculated Fᵣ to a critical value from the Chi-square distribution with (k-1) degrees of freedom. If Fᵣ is greater than the critical value, reject the null hypothesis [75].
The Scientist's Toolkit: Research Reagent Solutions
This table outlines key conceptual "reagents" for designing a robust materials search experiment.
| Item | Function in the Context of Search Algorithms |
|---|---|
| Non-parametric Tests | Statistical methods like Wilcoxon and Friedman used when data cannot assume a normal distribution, crucial for analyzing performance metrics of novel algorithms [77] [75]. |
| Paired Experimental Design | A setup where each algorithm is tested on the exact same set of problems/datasets, controlling for external variance and enabling the use of powerful paired tests like Wilcoxon [77]. |
| Blocking Factor | A variable (e.g., different material classes or datasets) used in the Friedman test to control for a known source of variability, increasing the sensitivity of the test to true differences between algorithms [75] [76]. |
| Bonferroni Correction | A conservative method to adjust the significance level (alpha) when performing multiple statistical tests simultaneously, controlling the family-wise error rate during post-hoc analysis [75] [79]. |
| Exploration-Exploitation Trade-off | A core concept in search where exploration tests new, uncertain regions of the search space, while exploitation refines known good solutions; statistical tests help evaluate the success of this balance [15] [5]. |
Frequently Asked Questions
Q1: What is the exploration-exploitation balance in the context of biomaterials design? In metaheuristic algorithms used for biomaterials optimization, exploration involves broadly searching the parameter space (e.g., different material compositions and structures) to discover promising new regions. Exploitation intensively refines searches in these promising areas to find the optimal solution [80]. An imbalance—too much exploration slows convergence, while too much exploitation traps algorithms in local optima, potentially missing the best material design [80].
Q2: How can a greedy selection strategy negatively impact my biomaterial optimization? A greedy selection strategy, which only accepts new solutions that are better than the current one, increases the risk of premature convergence [81]. The algorithm can become stuck in a local optimum—a good but not the best possible material configuration—and fail to explore other potentially superior designs [81].
Q3: My algorithm converges quickly but the solution is poor. What might be wrong? This is a classic sign of an under-explored search space, where the algorithm's exploitation overpowers exploration [80]. It may also indicate a need for more diverse initial population generation or the inclusion of mechanisms to help the algorithm escape local optima, such as the memory and evolutionary operators used in MEASSA [81].
Q4: Why is a clear definition of "biocompatibility" important for data-driven biomaterials research? Ambiguous definitions make consistent data extraction and learning difficult [82]. A unified, computationally friendly definition enables artificial intelligence (AI) and text mining tools to automatically profile the safety and effectiveness of new biomaterials from vast scientific literature and clinical data, accelerating discovery [82].
Q5: What are the key input parameters when designing a biomaterial? Inputs are divided into chemical and physical parameters [83]. Key examples are in the table below.
| Category | Input Parameter | Influence on Output Property |
|---|---|---|
| Chemical | Specific chemical moieties (e.g., pH-switchable groups) | Responsiveness to the biological environment [83] |
| Chemical | Surface charge | Polymer-gene interactions for gene delivery; antimicrobial properties [83] |
| Chemical | Targeting ligands (e.g., folic acid) | Organ or cancer cell targeting [83] |
| Physical | Microstructure | Crack propagation resistance and overall materials improvement [83] |
| Physical | Particle size | Enhanced permeability and retention (EPR) effect for nanoparticles; reduced fibrosis for larger microparticles [83] |
| Physical | Surface topology | Selective enrichment of cells and direction of cell differentiation [83] |
Q6: What quantitative metrics can I use to evaluate the performance of a tuning algorithm like MEASSA? A common metric is the Integral Absolute Error (IAE), which measures the absolute difference between the desired system response and the actual response over time [81]. A lower IAE indicates better performance. For biomaterials, success metrics include improved cell adhesion, reduced fibrotic response, or achieving specific organ targeting [83].
Troubleshooting Guides
Problem: Algorithm Premature Convergence
Symptoms
- The algorithm's performance stagnates early in the process.
- It consistently converges to the same suboptimal solution from different starting points.
- Lack of diversity in the population of candidate solutions.
Solution Implement an enhanced algorithm variant that improves the balance between global and local search. The MEASSA framework provides a proven methodology [81].
Experimental Protocol
- Integrate a Memory Mechanism: Maintain a separate, updated archive of the best solutions (elites) found during the search. This prevents valuable information from being lost and allows for a more focused search around these promising areas [81].
- Introduce an Evolutionary Operator: Use a guided strategy like Differential Evolution for population dynamics. This operator should use adaptive mutation and crossover to encourage diversity in early stages (exploration) and fine-tune solutions later (exploitation) [81].
- Apply a Stochastic Local Search: Intensively refine high-quality solutions from the memory archive. This search should adaptively generate trial solutions around the nearest neighbors of selected individuals to enhance exploitation and stabilize convergence [81].
Problem: Handling Multi-dimensional Biomaterials Data
Symptoms
- Difficulty in establishing a clear relationship between input parameters (e.g., composition, structure) and output properties (e.g., biological response).
- The optimization process is slow and computationally expensive due to the large number of possible parameter combinations.
Solution Leverage supervised machine learning to model the complex, non-linear relationships in biomaterials data [83].
Experimental Protocol
- Data Collection: Create a dataset where the inputs are material parameters (see FAQ table) and the outputs are the resulting properties. This data can come from high-throughput experiments or existing databases [83].
- Model Training: Feed this data into a supervised learning algorithm. The goal is to train a model that learns a function to reliably predict output properties from a set of input parameters [83].
- Validation and Prediction: Use the trained model to predict the properties of new, untested material compositions. This drastically accelerates the discovery process by prioritizing the most promising candidates for experimental validation [83]. For example, this approach can reduce the time for optimizing composite materials from several days to just a few hours [83].
Experimental Performance Data
The following table summarizes quantitative results from evaluating the enhanced MEASSA algorithm on three distinct dynamic systems, demonstrating its robustness for controller tuning [81].
| System Under Test | Key Performance Metric (IAE) | MEASSA's Performance | Demonstrated Advantage |
|---|---|---|---|
| DC Motor | Integral Absolute Error (IAE) | 9.977 (Lowest achieved) | Outperformed benchmark algorithms like PSO and GWO [81] |
| Three-Tank Liquid Level System | Integral Absolute Error (IAE) | 9.0781 (Lowest achieved) | Superior performance in a multi-variable fluid system [81] |
| Fourth-Order System | Integral Absolute Error (IAE) | 9.697 (Lowest achieved) | Effective control in a complex, high-order system [81] |
The Scientist's Toolkit: Essential Research Reagents & Materials
This table lists key components used in data-driven biomaterials research as highlighted in the search results.
| Item / Reagent | Function in Research |
|---|---|
| Polymeric Materials (e.g., PLGA) | Widely used for drug delivery depots and tissue engineering scaffolds due to their biocompatibility and tunable biodegradation kinetics [83]. |
| Metallic Alloys | Used for implants requiring high mechanical strength and relative inertness. Input parameters like composition are optimized to control properties like hardness and corrosion resistance [83]. |
| Ceramics (e.g., Hydroxyapatite) | Utilized as dental implants and in bone regeneration due to their ability to encourage bone development and osseointegration [83]. |
| Chemical Moieties (e.g., bisphosphonate) | Act as targeting ligands to improve binding to specific biological sites, such as bone tissue [83]. |
| High-Throughput Screening Platforms | Automated systems that generate large amounts of multi-dimensional data on material properties and biological responses, providing the essential dataset for machine learning models [83]. |
Methodology Visualization
The following diagram illustrates the integrated workflow of an enhanced metaheuristic algorithm, like MEASSA, applied to a biomaterials design problem.
Biomaterials Algorithm Workflow
Conclusion
Mastering the exploration-exploitation balance is not a one-size-fits-all endeavor but a dynamic process essential for advancing materials search in drug development. Synthesizing the key insights, successful strategies integrate adaptive control mechanisms, robust escape functions for local optima, and rigorous, multi-faceted validation. Future directions point towards greater integration of AI-driven predictive modeling and reinforcement learning to create self-adjusting algorithms. For biomedical research, these advancements promise to significantly accelerate the discovery of novel therapeutic materials and optimize drug development pipelines, ultimately reducing time and cost from bench to bedside.
References
- 1. Tackling Blind Spot Challenges in Metaheuristics ... [https://www.mdpi.com/2227-7390/13/10/1580]
- 2. Rapid discovery of promising materials via active learning ... [https://www.sciencedirect.com/science/article/abs/pii/S2352492823019360]
- 3. Hare escape optimization algorithm with applications in ... [https://www.nature.com/articles/s41598-025-10289-3]
- 4. Machine learning in materials informatics: recent ... [https://www.nature.com/articles/s41524-017-0056-5]
- 5. Trade-offs between Exploration and Exploitation in Local ... [https://www.geeksforgeeks.org/artificial-intelligence/trade-offs-between-exploration-and-exploitation-in-local-search-algorithms/]
- 6. Balancing exploration and exploitation in multiobjective ... [https://www.sciencedirect.com/science/article/abs/pii/S0020025519304499]
- 7. Multi-armed bandit [https://en.wikipedia.org/wiki/Multi-armed_bandit]
- 8. The Multi-Armed Bandit Problem and Its Solutions | Lil'Log [https://lilianweng.github.io/posts/2018-01-23-multi-armed-bandit/]
- 9. Implementing Multi-Armed Bandits: A Beginner's Hands-on ... [https://medium.com/@Nomidl/implementing-multi-armed-bandits-a-beginners-hands-on-guide-b4aed34f2075]
- 10. Materials Informatics 2025-2035: Markets, Strategies, Players [https://www.idtechex.com/en/research-report/materials-informatics-2025/1096]
- 11. Contextual Bandits In Drug Discovery [https://www.meegle.com/en_us/topics/contextual-bandits/contextual-bandits-in-drug-discovery]
- 12. New Algorithm Predicts Optimal Materials among All ... [https://www.labmanager.com/new-algorithm-predicts-optimal-materials-among-all-possible-compounds-22718]
- 13. Application of multi-armed bandits to dose-finding clinical ... [https://www.sciencedirect.com/science/article/abs/pii/S0933365723002270]
- 14. Multi-armed Bandit Models for the Optimal Design ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC4856206/]
- 15. Exploration and Exploitation During Sequential Search [https://pmc.ncbi.nlm.nih.gov/articles/PMC3403695/]
- 16. Artificial Intelligence (AI) Applications in Drug Discovery and ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11510778/]
- 17. Computational approaches streamlining drug discovery [https://www.nature.com/articles/s41586-023-05905-z]
- 18. Artificial intelligence revolution in drug discovery [https://www.sciencedirect.com/science/article/pii/S037851732500626X]
- 19. Drug Discovery Assays Support—Troubleshooting [https://www.thermofisher.com/us/en/home/technical-resources/technical-reference-library/drug-discovery-development-support-center/drug-discovery-assays-support/drug-discovery-assays-support-troubleshooting.html]
- 20. Multi-Armed Bandit: Study of Exploration vs. Exploitation [https://exploratiojournal.com/multi-armed-bandit-study-of-exploration-vs-exploitation/]
- 21. ε-Greedy, Annealing, and UCB - Reinforcement Learning [https://rl-book.com/learn/bandits/exploration_comparison/]
- 22. Bandit Algorithms - SCIP Doxygen Documentation [https://www.scipopt.org/doc-5.0.1/html/group__PublicBanditMethods.php]
- 23. Reinforcement Learning I: Multi-Armed Bandits [https://medium.com/@david-de-villiers/mastering-the-multi-armed-bandit-problem-in-reinforcement-learning-b4206700b779]
- 24. Multi-Armed Bandits [https://cse442-17f.github.io/LinUCB/]
- 25. The Upper Confidence Bound (UCB) Bandit Algorithm [https://towardsdatascience.com/the-upper-confidence-bound-ucb-bandit-algorithm-c05c2bf4c13f/]
- 26. A Comparison of Bandit Algorithms [https://towardsdatascience.com/a-comparison-of-bandit-algorithms-24b4adfcabb/]
- 27. Solving Multi-arm Bandits with Python [https://www.analyticsvidhya.com/blog/2023/02/solving-multi-arm-bandits-with-python/]
- 28. Evolution and Trends of the Exploration–Exploitation ... [https://www.mdpi.com/2313-7673/10/8/517]
- 29. : a novel nature-inspired metaheuristic Raindrop ... optimizer algorithm [https://pubmed.ncbi.nlm.nih.gov/41034289/]
- 30. Balancing exploitation and exploration: A novel hybrid ... [https://www.sciencedirect.com/science/article/pii/S1364815222000470]
- 31. Applications of nature-inspired metaheuristic algorithms for ... [https://www.nature.com/articles/s41598-024-56670-6]
- 32. Diversity-based adaptive differential evolution algorithm for ... [https://www.sciencedirect.com/science/article/abs/pii/S2210650225000276]
- 33. An improved FOX optimization algorithm using adaptive ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12445531/]
- 34. Adaptive Strategy Management: A new framework for large ... [https://www.sciencedirect.com/science/article/pii/S0045782525005286]
- 35. Active learning in materials science with emphasis on ... [https://www.nature.com/articles/s41524-019-0153-8]
- 36. Optimizing and Testing an Individualized and Adaptive ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12397713/]
- 37. An improved FOX optimization algorithm using adaptive ... [https://journals.plos.org/plosone/article?id=10.1371/journal.pone.0331965]
- 38. An Improved FOX Optimization Algorithm Using Adaptive ... [https://arxiv.org/html/2504.09574v2]
- 39. Advancements in Molecular Property Prediction: A Survey ... [https://arxiv.org/html/2408.09461v1]
- 40. Molecular property prediction based on graph structure ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11112045/]
- 41. A Gentle Introduction to Premature Convergence [https://www.machinelearningmastery.com/premature-convergence/]
- 42. A comparative review of approaches to prevent premature ... [https://www.sciencedirect.com/science/article/abs/pii/S1568494614003901]
- 43. Divergence of character and premature convergence [https://www.sciencedirect.com/science/article/abs/pii/S002002551500729X]
- 44. Premature convergence – Knowledge and References [https://taylorandfrancis.com/knowledge/Engineering_and_technology/Biomedical_engineering/Premature_convergence/]
- 45. Stochastic hill climbing vs random-restart ... [https://stackoverflow.com/questions/49595577/stochastic-hill-climbing-vs-random-restart-hill-climbing-algorithms]
- 46. algorithms - Random restart technique definition [https://cs.stackexchange.com/questions/132896/random-restart-technique-definition]
- 47. Targeted materials discovery using Bayesian algorithm ... [https://www.nature.com/articles/s41524-024-01326-2]
- 48. Improved exploration–exploitation trade-off through ... [https://www.sciencedirect.com/science/article/pii/S0925231224016072]
- 49. Self-Adaptive Priority Correction for Prioritized Experience ... [https://www.mdpi.com/2076-3417/10/19/6925]
- 50. Prioritized Experience Replay (pER) [https://www.emergentmind.com/topics/prioritized-experience-replay-per]
- 51. A novel physically inspired optimization algorithm [https://www.sciencedirect.com/science/article/abs/pii/S0045794916000092]
- 52. The RL Debugging Checklist I Wish I Had Earlier [https://medium.com/@geoffrey.gvd/the-rl-debugging-checklist-i-wish-i-had-earlier-6b949ec534e9]
- 53. Debugging Reinforcement Learning Systems [https://andyljones.com/posts/rl-debugging.html]
- 54. Hyperparameter tuning - Academic skills [https://www.academic-skills.org/experimenting/hyperparameter-tuning]
- 55. 深度学习调优指南中文版 [https://github.com/schrodingercatss/tuning_playbook_zh_cn]
- 56. AI、机器学习在材料科学研究中能发挥哪些作用? [https://www.microsoft.com/en-us/research/articles/tie-yan-liu-linwang-wang/]
- 57. 深度学习笔记(十四)—— 超参数优化[Hyperparameter ... [https://blog.csdn.net/weixin_44120025/article/details/114677393]
- 58. 2025最强贝叶斯优化实战指南:从论文复现到真实数据集调优 [https://blog.csdn.net/gitblog_00071/article/details/151860531]
- 59. [论文审查] Adaptive Hyperparameter Optimization ... [https://www.themoonlight.io/zh/review/adaptive-hyperparameter-optimization-for-continual-learning-scenarios]
- 60. 利用NVIDIA ALCHEMI 实现AI 驱动材料发现的革命性突破 [https://developer.nvidia.cn/blog/revolutionizing-ai-driven-material-discovery-using-nvidia-alchemi/]
- 61. AutoML之超参数优化 - 赵大寳 [https://fuhailin.github.io/AutoML-Hyperpam-Optimize/]
- 62. 高瓴人工智能学院长聘教授孙浩团队在《自然-计算科学》发表 ... [https://news.ruc.edu.cn/1992804283788271617.html]
- 63. Benchmark Function - an overview | ScienceDirect Topics [https://www.sciencedirect.com/topics/computer-science/benchmark-function]
- 64. Evaluating the performance of meta-heuristic algorithms on ... [https://link.springer.com/article/10.1007/s00521-022-07788-z]
- 65. On the impact of the performance metric on efficient ... [https://www.sciencedirect.com/science/article/abs/pii/S0004370221001806]
- 66. Two Criteria for Performance Analysis of Optimization ... [https://arxiv.org/html/2410.21677v1]
- 67. Common experiment design pitfalls [https://www.statsig.com/perspectives/experiment-design-pitfalls]
- 68. Benchmark Functions for CEC 2022 Competition on ... [https://arxiv.org/abs/2201.00523]
- 69. Improved FOX Optimization Algorithm [https://arxiv.org/html/2504.09574v1]
- 70. Grey wolf optimization - Introduction [https://www.geeksforgeeks.org/machine-learning/grey-wolf-optimization-introduction/]
- 71. Particle swarm optimization [https://en.wikipedia.org/wiki/Particle_swarm_optimization]
- 72. A Gentle Introduction to Particle Swarm Optimization [https://www.machinelearningmastery.com/a-gentle-introduction-to-particle-swarm-optimization/]
- 73. A novel hybrid PSO–GWO algorithm for optimization problems | Engineering with Computers [https://link.springer.com/article/10.1007/s00366-018-0668-5]
- 74. Linear Population Reduction SHADE (LSHADE) [https://www.mathworks.com/matlabcentral/fileexchange/162951-linear-population-reduction-shade-lshade]
- 75. Friedman Test [https://www.geeksforgeeks.org/dsa/friedman-test/]
- 76. Friedman test [https://en.wikipedia.org/wiki/Friedman_test]
- 77. Wilcoxon Signed-Rank Test - an overview [https://www.sciencedirect.com/topics/mathematics/wilcoxon-signed-rank-test]
- 78. Choosing the Right Statistical Test | Types & Examples [https://www.scribbr.com/statistics/statistical-tests/]
- 79. Friedman test and Wilcoxon - Cross Validated [https://stats.stackexchange.com/questions/296858/friedman-test-and-wilcoxon]
- 80. Evolution and Trends of the Exploration–Exploitation Balance ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC12383399/]
- 81. Enhanced artificial satellite search algorithm with memory ... [https://www.nature.com/articles/s41598-025-24760-8]
- 82. Redefining biomaterial biocompatibility: challenges for ... [https://www.sciencedirect.com/science/article/pii/S0167779923002895]
- 83. Biomaterials by design: Harnessing data for future ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8628044/]